We use Cowrie to emulate an SSH and Telnet server for our honeypots. Cowrie is great software maintained by Michel Oosterhof [1]. The honeypot is a reasonable emulation of such a server, easy to maintain, and very feature-rich for even more advanced analysis. We only use it in its simplest form for our DShield sensor.
Monthly Archives: January 2024
A Batch File With Multiple Payloads, (Fri, Jan 26th)
Windows batch files (.bat) are often seen by people as very simple but they can be pretty complex or.. contain interesting encoded payloads! I found one that contains multiple payloads decoded and used by a Powershell process. The magic is behind how comments can be added to such files. The default (or very common way) is to use the "REM" keyword. But you can also use a double-colon:
Facebook AdsManager Targeted by a Python Infostealer, (Thu, Jan 25th)
VMware Skyline Advisor Pro Proactive Findings – January 2024 Edition
Tweet VMware Skyline Advisor Pro releases new proactive Findings every month. Findings are prioritized by trending issues in VMware Technical Support, issues raised through post escalation review, security vulnerabilities, issues raised from VMware engineering, and nominated by customers. For the month of January, we released 60 new Findings. Of these, there are 37 Findings based … Continued
The post VMware Skyline Advisor Pro Proactive Findings – January 2024 Edition appeared first on VMware Support Insider.
Update on Atlassian Exploit Activity , (Tue, Jan 23rd)
Exploit activity against Atlassian Confluence servers has exploded since we first discussed it yesterday. The combination of a simple-to-exploit vulnerability and a potential set of high-value targets makes this an ideal vulnerability for many attackers.
AWS Weekly Roundup — Amazon ECS, RDS for MySQL, EMR Studio, AWS Community, and more — January 22, 2024
As usual, a lot has happened in the Amazon Web Services (AWS) universe this past week. I’m also excited about all the AWS Community events and initiatives that are happening around the world. Let’s take a look together!
Last week’s launches
Here are some launches that got my attention:
Amazon Elastic Container Service (Amazon ECS) now supports managed instance draining – Managed instance draining allows you to gracefully shutdown workloads deployed on Amazon Elastic Compute Cloud (Amazon EC2) instances by safely stopping and rescheduling them to other, non-terminating instances. This new capability streamlines infrastructure maintenance, such as deploying a new AMI version, eliminating the need for custom solutions to shutdown instances without disrupting their workloads. To learn more, check out Nathan’s post on the AWS Containers Blog.
Amazon Relational Database Service (Amazon RDS) for MySQL now supports multi-source replication – Using multi-source replication, you can configure multiple RDS for MySQL database instances as sources for a single target database instance. This feature facilitates tasks such as merging shards into a single target, consolidating data for analytics, or creating long-term backups within a single RDS for MySQL instance. The Amazon RDS for MySQL User Guide has all the details.
Amazon EMR Studio now comes with simplified create experience and improved start times – With the simplified console experience for creating EMR Studio, you can launch interactive and batch workloads with default settings more easily. The improved start times let you launch EMR Studio Workspaces for performing interactive analysis in notebooks in seconds. Have a look at the Amazon EMR User Guide to learn more.
For a full list of AWS announcements, be sure to keep an eye on the What’s New at AWS page.
Other AWS news
Here are some additional projects, programs, and news items that you might find interesting:
 Summarize news using Amazon Bedrock – My colleague Danilo built this application to summarize the most recent news from an RSS or Atom feed using Amazon Bedrock. The application is deployed as an AWS Lambda function. The function downloads the most recent entries from an RSS or Atom feed, downloads the linked content, extracts text, and makes a summary.
Summarize news using Amazon Bedrock – My colleague Danilo built this application to summarize the most recent news from an RSS or Atom feed using Amazon Bedrock. The application is deployed as an AWS Lambda function. The function downloads the most recent entries from an RSS or Atom feed, downloads the linked content, extracts text, and makes a summary.
 AWS Community Builders program – Interested in joining our AWS Community Builders program? The 2024 application is open until January 28. The AWS Community Builders program offers technical resources, education, and networking opportunities to AWS technical enthusiasts who are passionate about sharing knowledge and connecting with the technical community.
AWS Community Builders program – Interested in joining our AWS Community Builders program? The 2024 application is open until January 28. The AWS Community Builders program offers technical resources, education, and networking opportunities to AWS technical enthusiasts who are passionate about sharing knowledge and connecting with the technical community.
 AWS User Groups – The AWS User Group Yaounde Cameroon embarked on a 12-week workshop challenge. Over 12 weeks, participants explored various aspects of AWS and cloud computing, including architecture, security, storage, and more, to develop skills and share knowledge. You can read more about this amazing initiative in this LinkedIn post.
AWS User Groups – The AWS User Group Yaounde Cameroon embarked on a 12-week workshop challenge. Over 12 weeks, participants explored various aspects of AWS and cloud computing, including architecture, security, storage, and more, to develop skills and share knowledge. You can read more about this amazing initiative in this LinkedIn post.
AWS open-source news and updates – My colleague Ricardo writes this weekly open source newsletter in which he highlights new open source projects, tools, and demos from the AWS Community.
Upcoming AWS events
Check your calendars and sign up for these AWS events:
 AWS Innovate: AI/ML and Data Edition – Register now for the Asia Pacific & Japan AWS Innovate online conference on February 22, 2024, to explore, discover, and learn how to innovate with artificial intelligence (AI) and machine learning (ML). Choose from over 50 sessions in three languages and get hands-on with technical demos aimed at generative AI builders.
AWS Innovate: AI/ML and Data Edition – Register now for the Asia Pacific & Japan AWS Innovate online conference on February 22, 2024, to explore, discover, and learn how to innovate with artificial intelligence (AI) and machine learning (ML). Choose from over 50 sessions in three languages and get hands-on with technical demos aimed at generative AI builders.
 AWS Community re:Invent re:Caps – Join a Community re:Cap event organized by volunteers from AWS User Groups and AWS Cloud Clubs around the world to learn about the latest announcements from AWS re:Invent.
AWS Community re:Invent re:Caps – Join a Community re:Cap event organized by volunteers from AWS User Groups and AWS Cloud Clubs around the world to learn about the latest announcements from AWS re:Invent.
You can browse all upcoming in-person and virtual events.
That’s all for this week. Check back next Monday for another Weekly Roundup!
— Antje
This post is part of our Weekly Roundup series. Check back each week for a quick roundup of interesting news and announcements from AWS!
More Scans for Ivanti Connect "Secure" VPN. Exploits Public, (Thu, Jan 18th)
Exploits around the Ivanti Connect "Secure" VPN appliance, taking advantage of CVE-2023-46805, continue evolving. Late on Tuesday, more details became public, particularly the blog post by Rapid7 explaining the underlying vulnerability in depth [1]. Rapid7 also does a good job walking you through how Ivanti obfuscates the LUKS key in its appliance. This will make it easier for security researchers to inspect the code, hopefully pointing out additional vulnerabilities to Ivanti in the future. In other words, get ready for more Ivanti exploits, and hopefully patches, this year.
AWS Supply Chain update: Three new modules supporting upstream activities
 We are launching three new modules for AWS Supply Chain today. These modules are designed to help you collaborate with your suppliers across all tiers of your supply chain, with the goal of helping you to maintain optimum inventory levels at each site in the chain. Here’s an overview:
We are launching three new modules for AWS Supply Chain today. These modules are designed to help you collaborate with your suppliers across all tiers of your supply chain, with the goal of helping you to maintain optimum inventory levels at each site in the chain. Here’s an overview:
Supply Planning – This module helps you to accurately forecast and plan purchases of raw materials, components, and finished goods. It uses multiple algorithms to create supply plans that include purchase orders and inventory transfer requirements.
N-Tier Visibility – This module extends visibility and collaboration beyond your enterprise’s internal systems to multiple external tiers of trading partners.
Sustainability – this module creates a more secure and efficient way for you to request, collect, and review data for carbon emissions, as well as reports on hazardous material used in the acquisition, manufacturing, transportation, and disposal of goods. You can now send data requests to multiple tiers of trading partners, track responses, send reminders to absentees, and provide a central repository to store and view responses.
Let’s take a look at each one…
Supply Planning
AWS Supply Chain already includes a Demand Planning module which uses proprietary machine learning algorithms to forecast demand and generate a demand plan that is based on two or more years of historical order line data. The forecasts are granular and specific, including distribution centers and retail outlets.
The new Supply Planning module uses the demand plan as an input. It looks at existing inventory, accounts for uncertainties, and supports additional business input including stocking strategies, ultimately generating purchase orders for components and raw materials, ready for review and approval. Here is the main page of the Supply Planning module:
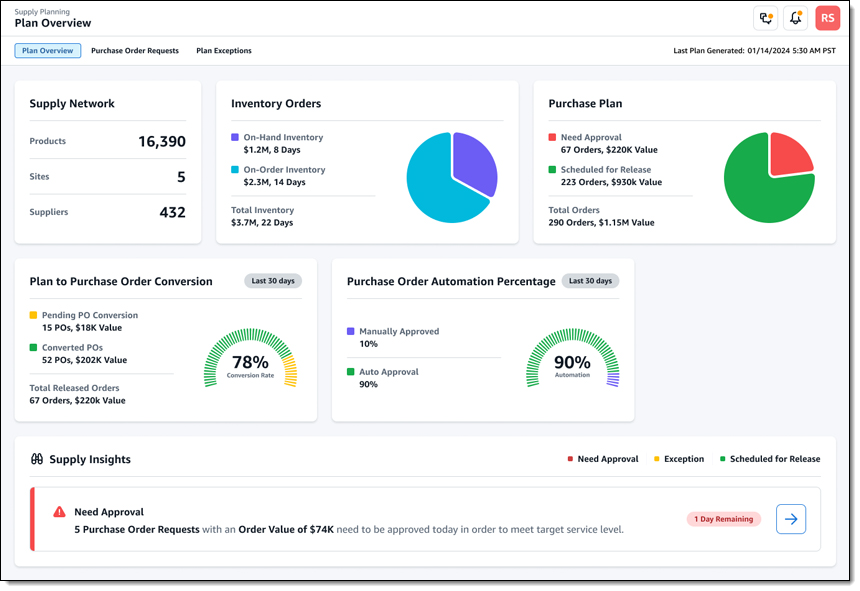
The module also supports auto replenishment and manufacturing plans. The manufacturing plans work backward from a Bill of Materials (BoM) which is broken down (exploded) into individual components that are sourced from multiple direct and indirect upstream sources.
Supply Planning is done with respect to a planning horizon and on a plan schedule, both of which are defined in the organization profile:
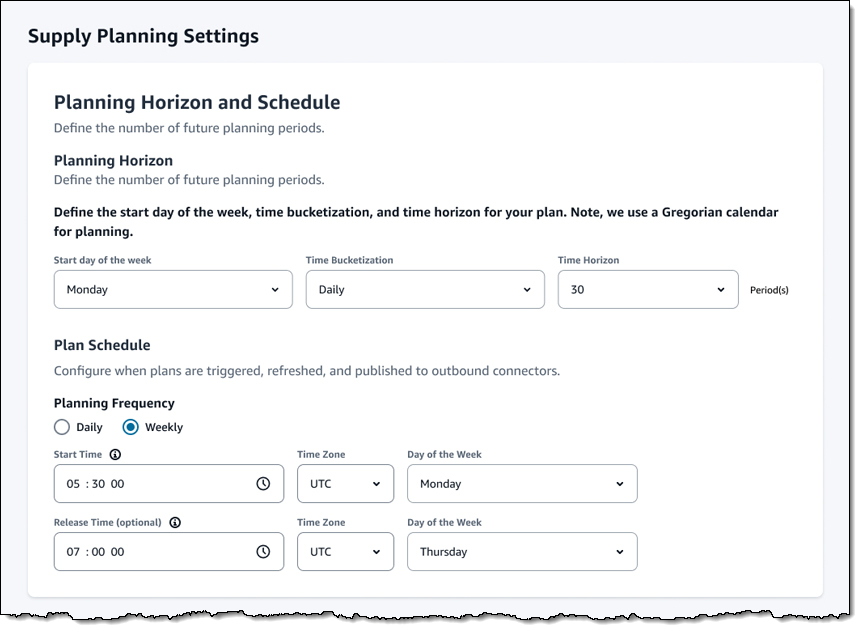
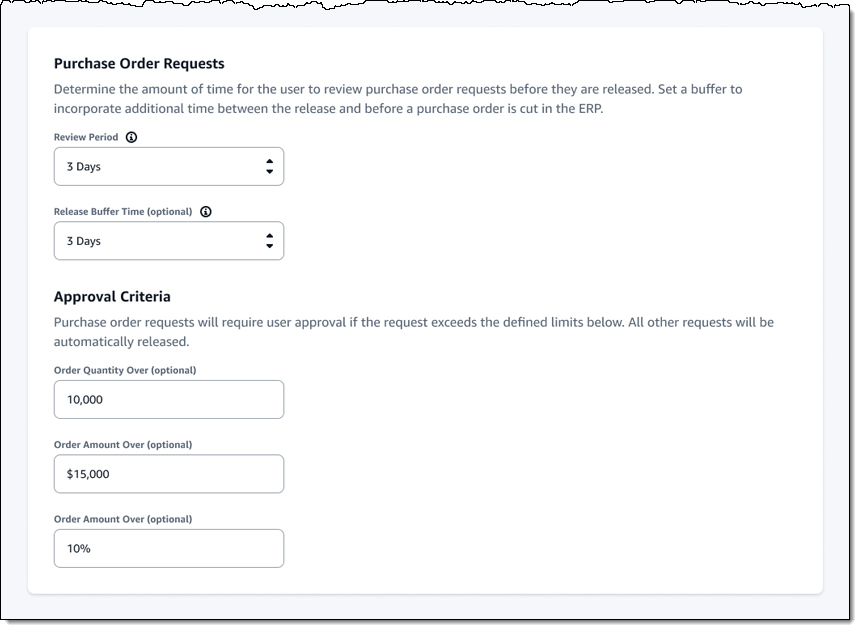
The settings for this module also allow for customization of purchase order review and approval:
N-Tier Visibility
This module helps you to work in a collaborative fashion with your vendors, the vendors that supply your vendors, and so forth. It automatically detects vendors and sets them up for on-boarding into AWS Supply Chain. The module supports manual and EDI-powered collaboration on purchase orders, while also helping to identify discrepancies and risks, and to find substitute vendors if necessary.
The main page of the module displays an overview of my trading partners:
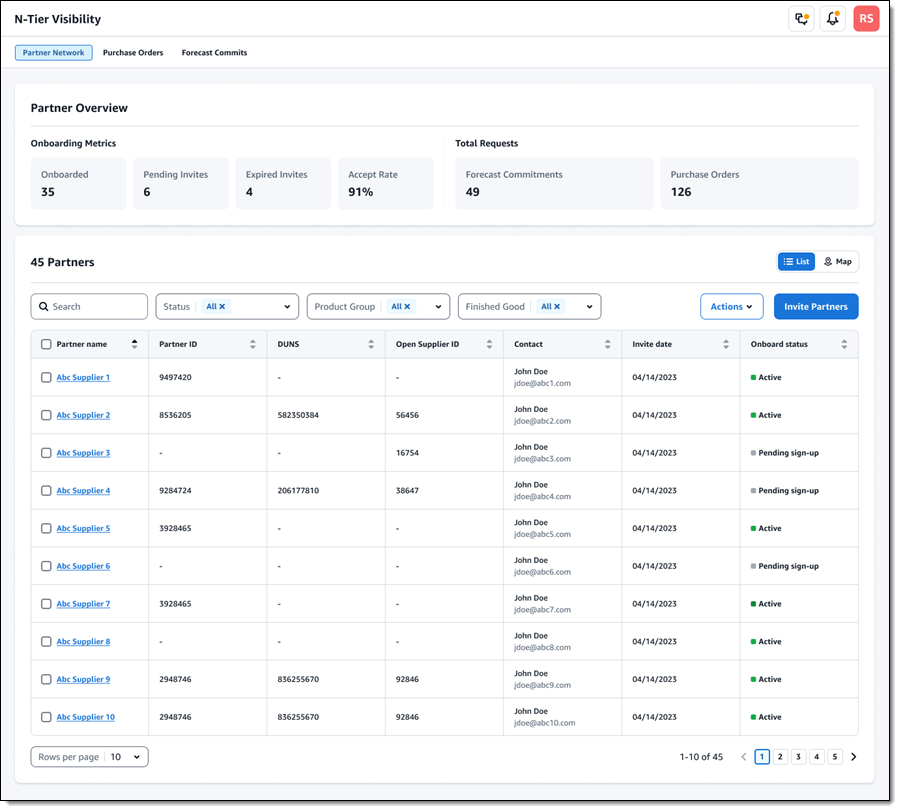
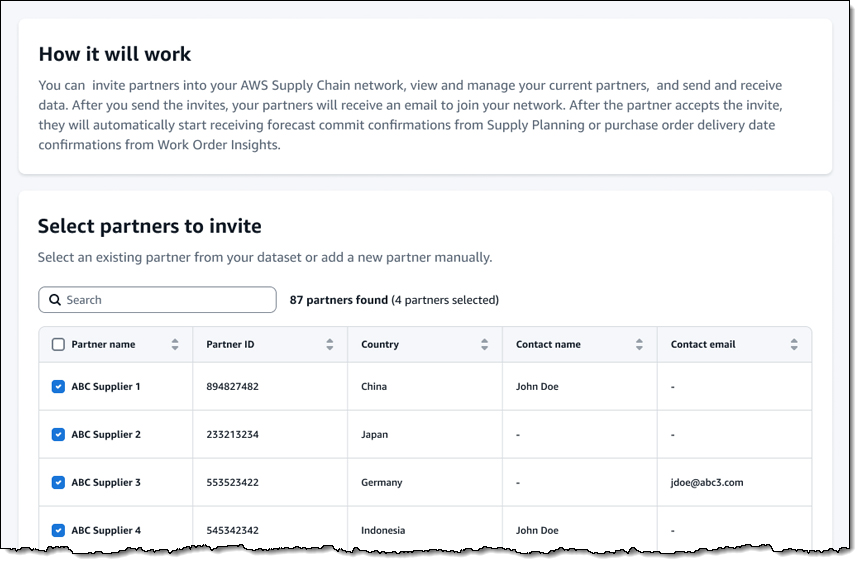
The Portal status column indicates that some of these partners have already onboarded, others have been invited (and one let the invite expire), and others have yet to be invited. I can click Invite partners to extend invitations. I select the partners (these have generally been auto-discovered using data in the Supply Chain Data Lake), and click Continue:
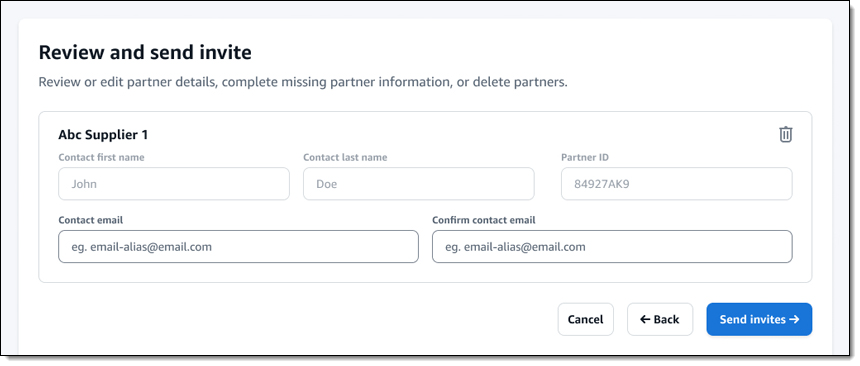
Then I enter the contact information for each partner that I selected, and click Send invites:
The contact receives an invitation via email and can then accept the invite. After they have accepted, they can receive and respond to supply plans and purchase orders electronically (via email or EDI).
Sustainability
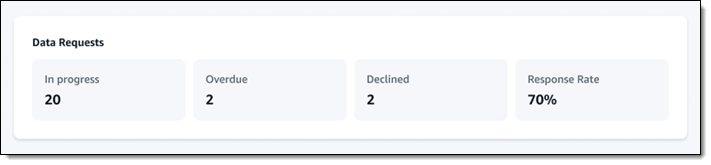
The Sustainability module helps you to request, receive, and review compliance and sustainability data from your partners. It builds on the partner network that I already described, and tracks requests for data:
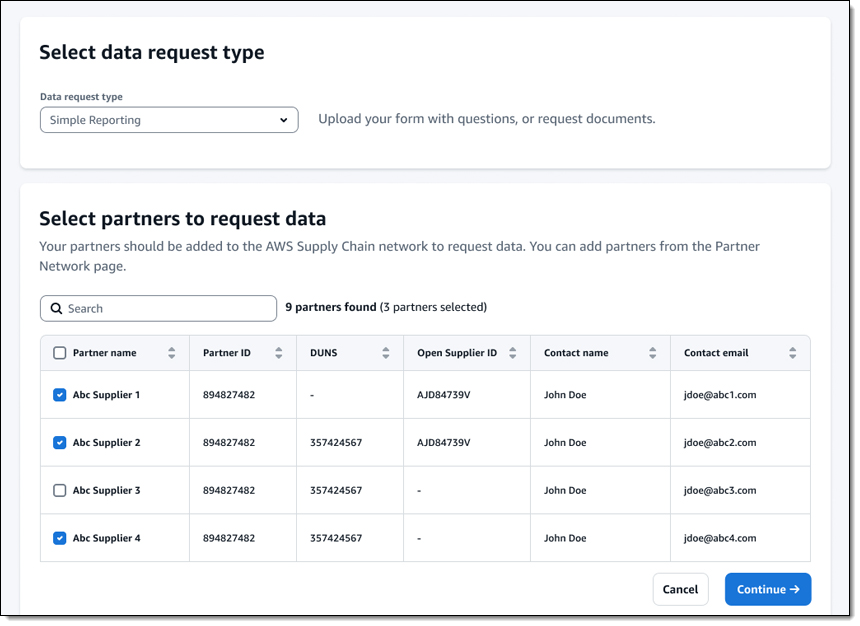
To request data, I select the type of data that I need and the partners that I need it from, then click Continue:
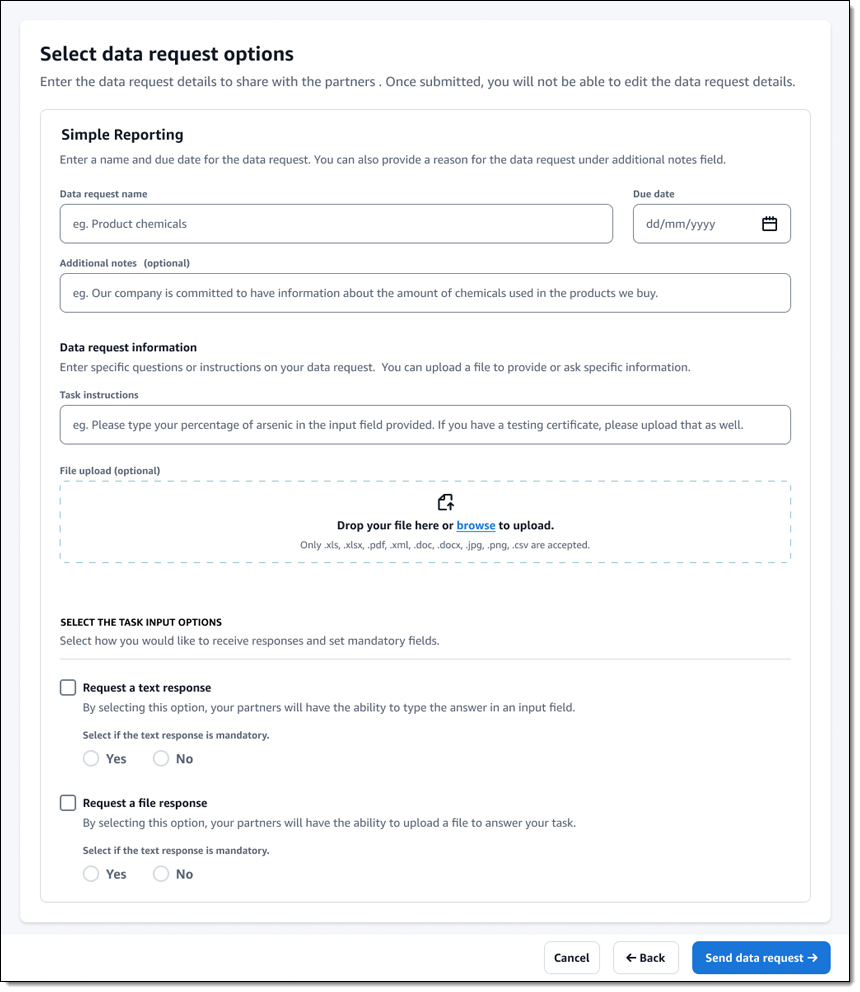
Then I enter the details that define my request, including a due date. I can ask the chosen partners for a text response and/or a file response:
The responses and files provided by each partner are written to the Supply Chain Data Lake and can also be exported to an Amazon Simple Storage Service (Amazon S3) bucket.
AWS Supply Chain Resources
If you are new to AWS Supply Chain and would like to learn more, here are some resources to get you started:
- AWS Supply Chain – Home page.
- AWS Supply Chain Now Generally Available – Mitigate Risks and Lower Costs with Increased Visibility and Actionable Insights – Blog post.
- AWS Supply Chain announces new upstream capabilities – Blog post.
- Improving demand planning for products with varying lifecycles with AWS Supply Chain – Blog post.
- AWS Supply Chain: Helping Woodside Energy optimize their supply chain – Video.
— Jeff;
Skyline Advisor Pro: Introducing Inventory Export Reports
Tweet You’ve asked for the ability to export inventory information, including licensing, and we’ve listened. The Skyline Team is proud to introduce this highly requested feature, Inventory Export Reports. Inventory Export Reports allow you to generate reports on your inventory, licensing, and configuration data. These reports can help you to identify potential problems, track changes … Continued
The post Skyline Advisor Pro: Introducing Inventory Export Reports appeared first on VMware Support Insider.
Known Indicators of Compromise Associated with Androxgh0st Malware
SUMMARY
The Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA) are releasing this joint Cybersecurity Advisory (CSA) to disseminate known indicators of compromise (IOCs) and tactics, techniques, and procedures (TTPs) associated with threat actors deploying Androxgh0st malware. Multiple, ongoing investigations and trusted third party reporting yielded the IOCs and TTPs, and provided information on Androxgh0st malware’s ability to establish a botnet that can further identify and compromise vulnerable networks.
The FBI and CISA encourage organizations to implement the recommendations in the Mitigations section of this CSA to reduce the likelihood and impact of cybersecurity incidents caused by Androxgh0st infections.
Download the PDF version of this report:
TECHNICAL DETAILS
Note: This advisory uses the MITRE ATT&CK® for Enterprise framework, version 14. See the MITRE ATT&CK Tactics and Techniques section for a table of the threat actors’ activity mapped to MITRE ATT&CK tactics and techniques with corresponding mitigation and/or detection recommendations. For assistance with mapping malicious cyber activity to the MITRE ATT&CK framework, see CISA and MITRE ATT&CK’s Best Practices for MITRE ATT&CK Mapping and CISA’s Decider Tool.
Overview
Androxgh0st malware has been observed establishing a botnet [T1583.005] for victim identification and exploitation in target networks. According to open source reporting[1], Androxgh0st is a Python-scripted malware [T1059.006] primarily used to target .env files that contain confidential information, such as credentials [T1552.001] for various high profile applications (i.e., Amazon Web Services [AWS], Microsoft Office 365, SendGrid, and Twilio from the Laravel web application framework). Androxgh0st malware also supports numerous functions capable of abusing the Simple Mail Transfer Protocol (SMTP), such as scanning [T1046] and exploiting exposed credentials [T1078] and application programming interfaces (APIs) [T1114], and web shell deployment [T1505.003].
Targeting the PHPUnit
Androxgh0st malware TTPs commonly involves the use of scripts, conducting scanning [T1595] and searching for websites with specific vulnerabilities. In particular, threat actors deploying Androxgh0st have been observed exploiting CVE-2017-9841 to remotely run hypertext preprocessor (PHP) code on fallible websites via PHPUnit [T1190]. Websites using the PHPUnit module that have internet-accessible (exposed) /vendor folders are subject to malicious HTTP POST requests to the /vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php uniform resource identifier (URI). This PHP page runs PHP code submitted through a POST request, which allows the threat actors to remotely execute code.
Malicious actors likely use Androxgh0st to download malicious files [T1105] to the system hosting the website. Threat actors are further able to set up a fake (illegitimate) page accessible via the URI to provide backdoor access to the website. This allows threat actors to download additional malicious files for their operations and access databases.
Laravel Framework Targeting
Androxgh0st malware establishes a botnet to scan for websites using the Laravel web application framework. After identifying websites using the Laravel web application, threat actors attempt to determine if the domain’s root-level .env file is exposed and contains credentials for accessing additional services. Note: .env files commonly store credentials and tokens. Threat actors often target .env files to steal these credentials within the environment variables.
If the .env file is exposed, threat actors will issue a GET request to the /.env URI to attempt to access the data on the page. Alternatively, Androxgh0st may issue a POST request to the same URI with a POST variable named 0x[] containing certain data sent to the web server. This data is frequently used as an identifier for the threat actor. This method appears to be used for websites in debug mode (i.e., when non-production websites are exposed to the internet). A successful response from either of these methods allows the threat actors to look for usernames, passwords, and/or other credentials pertaining to services such as email (via SMTP) and AWS accounts.
Androxgh0st malware can also access the application key [TA0006] for the Laravel application on the website. If the threat actors successfully identify the Laravel application key, they will attempt exploitation by using the key to encrypt PHP code [T1027.010]. The encrypted code is then passed to the website as a value in the cross-site forgery request (XSRF) token cookie, XSRF-TOKEN, and included in a future GET request to the website. The vulnerability defined in CVE-2018-15133 indicates that on Laravel applications, XSRF token values are subject to an un-serialized call, which can allow for remote code execution. In doing so, the threat actors can upload files to the website via remote access.
Apache Web Server Targeting
In correlation with CVE-2021-41773, Androxgh0st actors have been observed scanning vulnerable web servers [T1595.002] running Apache HTTP Server versions 2.4.49 or 2.4.50. Threat actors can identify uniform resource locators (URLs) for files outside root directory through a path traversal attack [T1083]. If these files are not protected by the “request all denied” configuration and Common Gateway Interface (CGI) scripts are enabled, this may allow for remote code execution.
If threat actors obtain credentials for any services using the above methods, they may use these credentials to access sensitive data or use these services to conduct additional malicious operations. For example, when threat actors successfully identify and compromise AWS credentials from a vulnerable website, they have been observed attempting to create new users and user policies [T1136]. Additionally, Andoxgh0st actors have been observed creating new AWS instances to use for conducting additional scanning activity [T1583.006].
INDICATORS OF COMPROMISE (IOCs)
Based on investigations and analysis, the following requests are associated with Androxgh0st activity:
- Incoming GET and POST requests to the following URIs:
/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php/.env
- Incoming POST requests with the following strings:
[0x%5B%5D=androxgh0st]ImmutableMultiDict([('0x[]', 'androxgh0st')])
In both previously listed POST request strings, the name androxgh0st has been observed to be replaced with other monikers.
Additional URIs observed by the FBI and a trusted third party used by these threat actors for credential exfiltration include:
/info/phpinfo/phpinfo.php/?phpinfo=1/frontend_dev.php/$/_profiler/phpinfo/debug/default/view?panel=config/config.json/.json/.git/config/live_env/.env.dist/.env.save/environments/.env.production/.env.production.local/.env.project/.env.development/.env.production/.env.prod/.env.development.local/.env.old//.env- Note: the actor may attempt multiple different potential URI endpoints scanning for the
.envfile, for example/docker/.env or /local/.env.
- Note: the actor may attempt multiple different potential URI endpoints scanning for the
/.aws/credentials/aws/credentials/.aws/config/.git/.test/admin/backend/app/current/demo/api/backup/beta/cron/develop/Laravel/laravel/core/gists/cache/test.php/info.php//.env/admin-app/.env%20/laravel/.env%20/shared/.env%20/.env.project%20/apps/.env%20/development/.env%20/live_env%20/.env.development%20
Targeted URIs for web-shell drop:
/.env/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//admin/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//api/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//backup/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//blog/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//cms/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//demo/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//dev/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//laravel/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//lib/phpunit/phpunit/src/Util/PHP/eval-stdin.php//lib/phpunit/phpunit/Util/PHP/eval-stdin.php//lib/phpunit/src/Util/PHP/eval-stdin.php//lib/phpunit/Util/PHP/eval-stdin.php//new/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//old/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//panel/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//phpunit/phpunit/src/Util/PHP/eval-stdin.php//phpunit/phpunit/Util/PHP/eval-stdin.php//phpunit/src/Util/PHP/eval-stdin.php//phpunit/Util/PHP/eval-stdin.php//protected/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//sites/all/libraries/mailchimp/vendor/phpunit/phpunit/src/Util/PHP/evalstdin.php//vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//vendor/phpunit/phpunit/Util/PHP/eval-stdin.php//vendor/phpunit/src/Util/PHP/eval-stdin.php//vendor/phpunit/Util/PHP/eval-stdin.php//wp-content/plugins/cloudflare/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//wp-content/plugins/dzs-videogallery/class_parts/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//wp-content/plugins/jekyll-exporter/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//wp-content/plugins/mm-plugin/inc/vendors/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php//www/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php/admin/ckeditor/plugins/ajaxplorer/phpunit/src/Util/PHP/eval-stdin.php/admin/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php/api/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php/api/vendor/phpunit/phpunit/src/Util/PHP/Template/eval-stdin.php/lab/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php/laravel/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php/laravel_web/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php/laravel52/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php/laravelao/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php/lib/phpunit/phpunit/src/Util/PHP/eval-stdin.php/lib/phpunit/phpunit/Util/PHP/eval-stdin.php/lib/phpunit/phpunit/Util/PHP/evalstdin.php%20/lib/phpunit/src/Util/PHP/eval-stdin.php/lib/phpunit/src/Util/PHP/eval-stdin.php/lib/phpunit/Util/PHP/eval-stdin.php/lib/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php/libraries/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php/phpunit/phpunit/src/Util/PHP/eval-stdin.php/phpunit/phpunit/Util/PHP/eval-stdin.php/phpunit/phpunit/Util/PHP/eval-stdin.php%20/phpunit/src/Util/PHP/evalstdin.php/phpunit/src/Util/PHP/eval-stdin.php./phpunit/Util/PHP/eval-stdin.php/phpunit/Util/PHP/eval-stdin.php%20/lib/phpunit/phpunit/src/Util/PHP/eval-stdin.php/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php.dev/vendor/phpunit/phpunit/Util/PHP/eval-stdin.php/vendor/phpunit/phpunit/Util/PHP/eval-stdin.php%20/vendor/phpunit/src/Util/PHP/eval-stdin.php/vendor/phpunit/src/Util/PHP/eval-stdin.php/vendor/phpunit/Util/PHP/eval-stdin.php/vendor/phpunit/Util/PHP/eval-stdin.php%20/phpunit/phpunit/src/Util/PHP/eval-stdin.php/yii/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php/zend/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
An example of attempted credential exfiltration through (honeypot) open proxies:
POST /.aws/credentials HTTP/1.1
host: www.example.com
user-agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/81.0.4044.129 Safari/537.36
accept-encoding: gzip, deflate
accept: */*
connection: keep-alive
content-length: 20
content-type: application/x-www-form-urlencoded
0x%5B%5D=androxgh0st
An example of attempted web-shell drop through (honeypot) open proxies:
GET http://www.example.com/lib/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php HTTP/1.1
host: www.example.com
user-agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/116.0.0.0 Safari/537.36 Edg/116.0.1938.76
accept-encoding: gzip, deflate
accept: */*
connection: keep-alive
x-forwarded-for: 200.172.238.135
content-length: 279
Monikers used instead of Androxgh0st (0x%5B%5D=???):
- Ridho
- Aws
- 0x_0x
- x_X
- nopebee7
- SMTPEX
- evileyes0
- privangga
- drcrypter
- errorcool
- drosteam
- androxmen
- crack3rz
- b4bbyghost
- 0x0day
- janc0xsec
- blackb0x
- 0x1331day
- Graber
Example malware drops through eval-stdin.php:
hxxps://mc.rockylinux[.]si/seoforce/triggers/files/evil.txt
59e90be75e51c86b4b9b69dcede2cf815da5a79f7e05cac27c95ec35294151f4
hxxps://chainventures.co[.]uk/.well-known/aas
dcf8f640dd7cc27d2399cce96b1cf4b75e3b9f2dfdf19cee0a170e5a6d2ce6b6
hxxp://download.asyncfox[.]xyz/download/xmrig.x86_64
23fc51fde90d98daee27499a7ff94065f7ed4ac09c22867ebd9199e025dee066
hxxps://pastebin[.]com/raw/zw0gAmpC
ca45a14d0e88e4aa408a6ac2ee3012bf9994b16b74e3c66b588c7eabaaec4d72
hxxp://raw.githubusercontent[.]com/0x5a455553/MARIJUANA/master/MARIJUANA.php
0df17ad20bf796ed549c240856ac2bf9ceb19f21a8cae2dbd7d99369ecd317ef
hxxp://45.95.147[.]236/tmp.x86_64
6b5846f32d8009e6b54743d6f817f0c3519be6f370a0917bf455d3d114820bbc
hxxp://main.dsn[.]ovh/dns/pwer
bb7070cbede294963328119d1145546c2e26709c5cea1d876d234b991682c0b7
hxxp://tangible-drink.surge[.]sh/configx.txt
de1114a09cbab5ae9c1011ddd11719f15087cc29c8303da2e71d861b0594a1ba
MITRE ATT&CK TACTICS AND TECHNIQUES
See Tables 1-10 for all referenced threat actor tactics and techniques in this advisory.
| Technique Title | ID | Use |
|---|---|---|
|
Active Scanning: Vulnerability Scanning |
The threat actor scans websites for specific vulnerabilities to exploit. |
| Technique Title | ID | Use |
|---|---|---|
|
Acquire Infrastructure: Botnet |
The threat actor establishes a botnet to identify and exploit victims. |
|
|
Acquire Infrastructure: Web Services |
The threat actor creates new AWS instances to use for scanning. |
| Technique Title | ID | Use |
|---|---|---|
|
Exploit Public-Facing Application |
The threat actor exploits CVE-2017-9841 to remotely run hypertext preprocessor (PHP) code on websites via PHPUnit. |
| Technique Title | ID | Use |
|---|---|---|
|
Command and Scripting Interpreter: Python |
The threat actor uses Androxgh0st, a Python-scripted malware, to target victim files. |
| Technique Title | ID | Use |
|---|---|---|
|
Valid Accounts |
The threat actor abuses the simple mail transfer protocol (SMTP) by exploiting exposed credentials. |
|
|
Server Software Component: Web Shell |
The threat actor deploys web shells to maintain persistent access to systems. |
|
|
Create Account |
The threat actor attempts to create new users and user policies with compromised AWS credentials from a vulnerable website. |
| Technique Title | ID | Use |
|
Obfuscated Files or Information: Command Obfuscation |
The threat actor can exploit a successfully identified Laravel application key to encrypt PHP code, which is then passed to the site as a value in the XSRF-TOKEN cookie. |
| Technique Title | ID | Use |
|
Credential Access |
The threat actor can access the application key of the Laravel application on the site. |
|
|
Unsecured Credentials: Credentials in Files |
The threat actor targets .env files that contain confidential credential information. |
| Technique Title | ID | Use |
|
File and Directory Discovery |
The threat actor can identify URLs for files outside root directory through a path traversal attack. |
|
|
Network Service Discovery |
The threat actor uses Androxgh0st to abuse simple mail transfer protocol (SMTP) via scanning. |
| Technique Title | ID | Use |
|
Email Collection |
The threat actor interacts with application programming interfaces (APIs) to gather information. |
| Technique Title | ID | Use |
|
Ingress Tool Transfer |
The threat actor runs PHP code through a POST request to download malicious files to the system hosting the website. |
MITIGATIONS
The FBI and CISA recommend implementing the mitigations below to improve your organization’s cybersecurity posture based on Androxgh0st threat actor activity. These mitigations align with the Cross-Sector Cybersecurity Performance Goals (CPGs) developed by CISA and the National Institute of Standards and Technology (NIST). The CPGs provide a minimum set of practices and protections that CISA and NIST recommend all organizations implement. CISA and NIST based the CPGs on existing cybersecurity frameworks and guidance to protect against the most common and impactful threats, tactics, techniques, and procedures. Visit CISA’s Cross-Sector Cybersecurity Performance Goals for more information on the CPGs, including additional recommended baseline protections.
These mitigations apply to all critical infrastructure organizations and network defenders. FBI and CISA recommend that software manufacturers incorporate secure by design principles and tactics into their software development practices, limiting the impact of actor techniques and strengthening their customers’ security posture. For more information on secure by design, see CISA’s Secure by Design webpage.
The FBI and CISA recommend network defenders apply the following mitigations to limit potential adversarial use of common system and network discovery techniques and to reduce the risk of compromise by actors using Androxgh0st malware.
- Keep all operating systems, software, and firmware up to date. Specifically, ensure that Apache servers are not running versions 2.4.49 or 2.4.50. Timely patching is one of the most efficient and cost-effective steps an organization can take to minimize its exposure to cybersecurity threats. Prioritize patching known exploited vulnerabilities in internet-facing systems.
- Verify that the default configuration for all URIs is to deny all requests unless there is a specific need for it to be accessible.
- Ensure that any live Laravel applications are not in “debug” or testing mode. Remove all cloud credentials from
.envfiles and revoke them. All cloud providers have safer ways to provide temporary, frequently rotated credentials to code running inside a web server without storing them in any file. - On a one-time basis for previously stored cloud credentials, and on an on-going basis for other types of credentials that cannot be removed, review any platforms or services that have credentials listed in the
.envfile for unauthorized access or use. - Scan the server’s file system for unrecognized PHP files, particularly in the root directory or
/vendor/phpunit/phpunit/src/Util/PHPfolder. - Review outgoing GET requests (via cURL command) to file hosting sites such as GitHub, pastebin, etc., particularly when the request accesses a
.phpfile.
VALIDATE SECURITY CONTROLS
In addition to applying mitigations, FBI and CISA recommend exercising, testing, and validating your organization’s security program against the threat behaviors mapped to the MITRE ATT&CK for Enterprise framework in this advisory. The authoring agencies recommend testing your existing security controls inventory to assess how they perform against the ATT&CK techniques described in this advisory.
To get started:
- Select an ATT&CK technique described in this advisory (see Tables 1-10).
- Align your security technologies against the technique.
- Test your technologies against the technique.
- Analyze your detection and prevention technologies’ performance.
- Repeat the process for all security technologies to obtain a set of comprehensive performance data.
- Tune your security program, including people, processes, and technologies, based on the data generated by this process.
FBI and CISA recommend continually testing your security program, at scale, in a production environment to ensure optimal performance against the MITRE ATT&CK techniques identified in this advisory.
REPORTING
The FBI encourages organizations to report information concerning suspicious or criminal activity to their local FBI field office. With regards to specific information that appears in this CSA, indicators should always be evaluated in light of an organization’s complete security situation.
When available, each report submitted should include the date, time, location, type of activity, number of people, and type of equipment used for the activity, the name of the submitting company or organization, and a designated point of contact. Reports can be submitted to the FBI Internet Crime Complaint Center (IC3), a local FBI Field Office, or to CISA via its Incident Reporting System or its 24/7 Operations Center at report@cisa.gov or (888) 282-0870.
RESOURCES
- CISA: Known Exploited Vulnerabilities Catalog
- CISA, MITRE: Best Practices for MITRE ATT&CK Mapping
- CISA: Decider Tool
- NIST: CVE-2017-9841
- NIST: CVE-2018-15133
- NIST: CVE-2021-41773
- CISA: Cross-Sector Cybersecurity Performance Goals
- CISA: Secure by Design
REFERENCES
ACKNOWLEDGEMENTS
Amazon contributed to this CSA.
DISCLAIMER
The information in this report is being provided “as is” for informational purposes only. FBI and CISA do not endorse any commercial entity, product, company, or service, including any entities, products, or services linked within this document. Any reference to specific commercial entities, products, processes, or services by service mark, trademark, manufacturer, or otherwise, does not constitute or imply endorsement, recommendation, or favoring by FBI and CISA.
VERSION HISTORY
January 16, 2024: Initial version.