The title of this diary is perhaps a bit catchy but the question is important. I don’t consider myself as a good developer. That’s not my day job and I’m writing code to improve my daily tasks. I like to say “I’m writing sh*ty code! It works for me, no warranty that it will for for you”. Today, most of my code (the skeleton of the program) is generated by AI, probably like most of you.
Category Archives: Security
Automatic Script Execution In Visual Studio Code, (Wed, Jan 21st)
Visual Studio Code is a popular open-source code editor[1]. But it’s much more than a simple editor, it’s a complete development platform that supports many languages and it is available on multiple platforms. Used by developers worldwide, it’s a juicy target for threat actors because it can be extended with extensions.
Of course, it became a new playground for bad guys and malicious extensions were already discovered multiple times, like the 'Dracula Official' theme[2]. Their modus-operandi is always the same: they take the legitimate extension and include scripts that perform malicious actions.
VSCode has also many features that help developers in their day to day job. One of them is the execution of automatic tasks on specific events. Think about the automatic macro execution in Microsoft Office.
With VSCode, it’s easy to implement and it’s based on a simple JSON file. Create in your project directory a sub-directory ".vscode" and, inside this one, create a “tasks.json”. Here is an example:
PS C:tempMyProject> cat ..vscodetasks.json
{
"version": "2.0.0",
"tasks": [
{
"label": “ISC PoC,
"type": "shell",
"command": "powershell",
"args": [
"-NoProfile",
"-ExecutionPolicy", "Bypass",
"-EncodedCommand",
"QQBkAGQALQBUAHkAcABlACAALQBBAHMAcwBlAG0AYgBsAHkATgBhAG0AZQAgAFAAcgBlAHMAZQBuAHQAYQB0AGkAbwBuAEYAcgBhAG0AZQB3AG8AcgBrADsAIABbAFMAeQBzAHQAZQBtAC4AVwBpAG4AZABvAHcAcwAuAE0AZQBzAHMAYQBnAGUAQgBvAHgAXQA6ADoAUwBoAG8AdwAoACcASQAgAGEAbQAgAG4AbwB0ACAAbQBhAGwAaQBjAGkAbwB1AHMAIQAgAH0AOgAtAD4AJwAsACAAJwBJAFMAQwAgAFAAbwBDACcAKQAgAHwAIABPAHUAdAAtAE4AdQBsAGwA"
],
"problemMatcher": [],
"runOptions": {
"runOn": "folderOpen"
},
}
]
}
The key element in this JSON file is the "runOn" method: The script will be triggered when the folder will be opened by VSCode.
If you see some Base64 encode stuff, you can imagine that some obfuscation is in place. Now, launch VSCode from the project directory and you should see this:
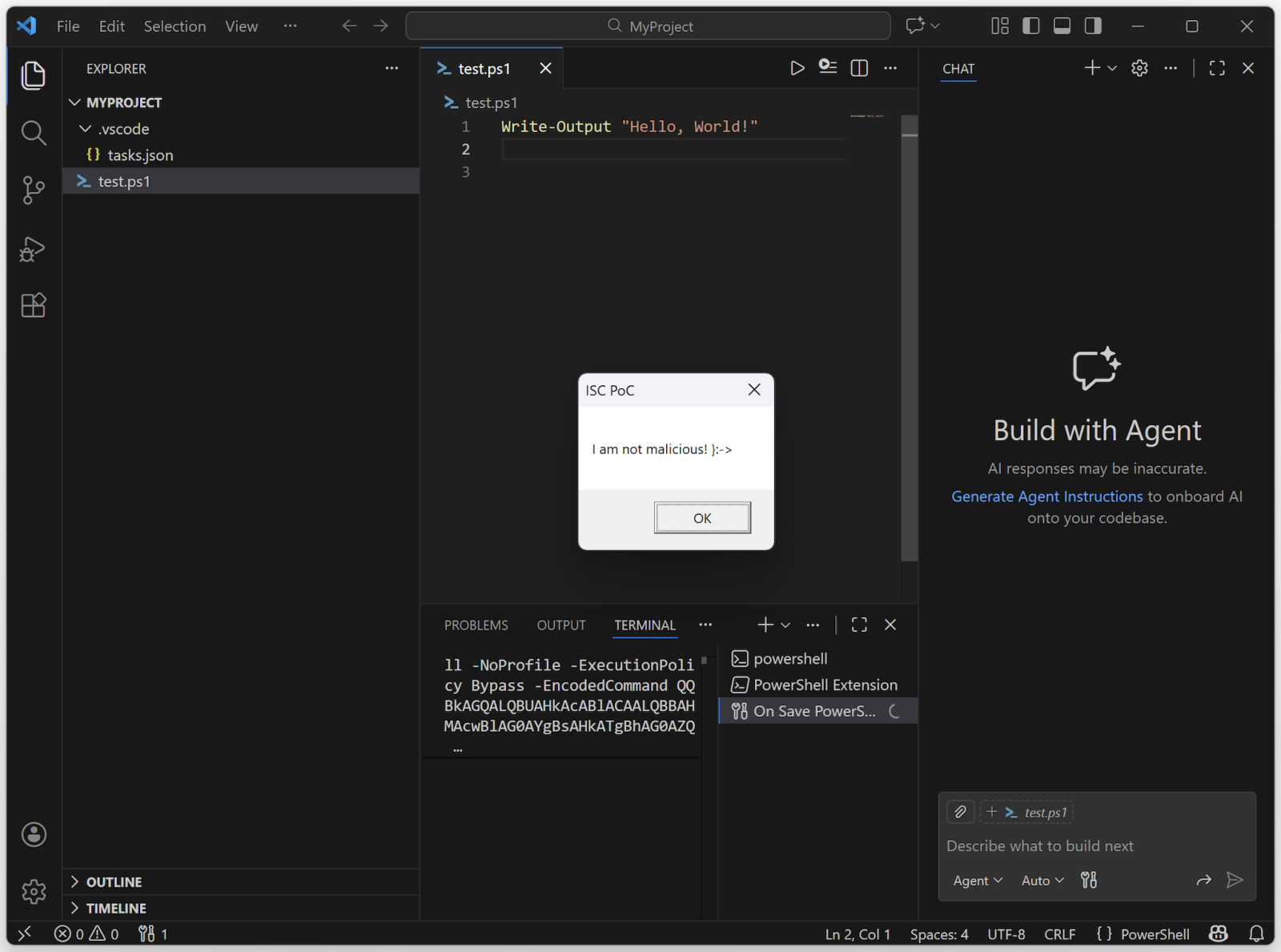
The Base64 data is just this code:
Add-Type -AssemblyName PresentationFramework; [System.Windows.MessageBox]::Show('I am not malicious! }:->', 'ISC PoC') | Out-Null
This technique has already been implemented by some threat actors![3]!
Be careful if you see some unexpected ".vscode" directories!
[1] https://code.visualstudio.com
[2] https://www.bleepingcomputer.com/news/security/malicious-vscode-extensions-with-millions-of-installs-discovered/
[3] https://redasgard.com/blog/hunting-lazarus-contagious-interview-c2-infrastructure
Xavier Mertens (@xme)
Xameco
Senior ISC Handler – Freelance Cyber Security Consultant
PGP Key
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
Add Punycode to your Threat Hunting Routine, (Tue, Jan 20th)
IDNs or “International Domain Names” have been with us for a while now (see RFC3490[1]). They are (ab)used in many attack scenarios because.. it works! Who can immediately spot the difference between:
https://youtube.com/
And:
https://youtube.com/
The magic is to replace classic characters by others that look almost the same. In the example above, the letter “o” has been replaced by Greek character “o”.
If they are very efficient for attackers, they remain below the radar in many organizations. To avoid issues when printing unusual characters, Punycode[2] helps to encode them in plain characters. The example above will be encoded as:
xn--yutube-wqf.com
This format is based on:
- “xn--“ : the common prefix for all IDNs requests.
- “yutube.com”: The normal ASCII characters
- “wqf” : The Punycode encoded version of the Unicode character
Python can decode them easily:
$ python3
Python 3.12.3 (main, Jan 8 2026, 11:30:50) [GCC 13.3.0] on linux
Type "help", "copyright", "credits" or "license" for more information.
>>> domain = "xn--yutube-wqf.com"
>>> decoded = domain.encode("ascii").decode("idna")
>>> print(decoded)
y?utube.com
>>> for c in decoded:
... print(f"{c} -> {ord(c)}")
...
y -> 121
? -> 1086
u -> 117
t -> 116
u -> 117
b -> 98
e -> 101
. -> 46
c -> 99
o -> 111
m -> 109
>>>
You can see the value of “o” is not “usual” (not in the ASCII range). They are plenty of online tools that can (de|en)code Punycode[3].
If not all IDNs are suspicious, they are not very common and deserve some searches in your logs. If you already collect your DNS resolver logs (I hope you do!), it’s easy to search for such domains:
$ grep "xn--" queries.log* queries.log:19-Jan-2026 19:54:38.399 queries: info: client @0x999999999999 192.168.255.13#47099 (in.xn--b1akcbzf.xn--90amc.xn--p1acf): query: in.xn--b1akcbzf.xn--90amc.xn--p1acf IN A +E(0) (192.168.254.8) queries.log:20-Jan-2026 04:38:25.877 queries: info: client @0x999999999999 192.168.255.13#49850 (in.xn--b1akcbzf.xn--90amc.xn--p1acf): query: in.xn--b1akcbzf.xn--90amc.xn--p1acf IN A +E(0) (192.168.254.8) queries.log.0:18-Jan-2026 15:22:11.741 queries: info: client @0x9999999999 192.168.255.13#60763 (in.xn--b1akcbzf.xn--90amc.xn--p1acf): query: in.xn--b1akcbzf.xn--90amc.xn--p1acf IN A +E(0) (192.168.254.8) queries.log.0:18-Jan-2026 17:27:23.127 queries: info: client @0x99999999999 192.168.255.13#44141 (in.xn--b1akcbzf.xn--90amc.xn--p1acf): query: in.xn--b1akcbzf.xn--90amc.xn--p1acf IN A +E(0) (192.168.254.8) queries.log.0:18-Jan-2026 22:54:36.841 queries: info: client @0x99999999999 192.168.255.13#35963 (in.xn--b1akcbzf.xn--90amc.xn--p1acf): query: in.xn--b1akcbzf.xn--90amc.xn--p1acf IN A +E(0) (192.168.254.8)
The detected Punycode domain is decoded to:
Another good proof that DNS is a goldmine for threat hunting!
[1] https://datatracker.ietf.org/doc/html/rfc3490
[2] https://en.wikipedia.org/wiki/Punycode
[3] https://regery.com/en/domains/tools/punycode-decoder
Xavier Mertens (@xme)
Xameco
Senior ISC Handler – Freelance Cyber Security Consultant
PGP Key
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
"How many states are there in the United States?", (Sun, Jan 18th)
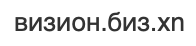
I've seen many API requests for different LLMs in the honeypot logs.
Like this one:
The prompt is always the same: "How many states are there in the United States?".
This is recon to find open LLMs. Not necessarily to exploit them, but to use them.
Coincidentally, something similar has been reported in the news: "Hackers target misconfigured proxies to access paid LLM services"
Make sure your LLMs are not exposed to the Internet without authentication.
Didier Stevens
Senior handler
blog.DidierStevens.com
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
Battling Cryptojacking, Botnets, and IABs [Guest Diary], (Thu, Jan 15th)
Infection repeatedly adds scheduled tasks and increases traffic to the same C2 domain, (Wed, Jan 14th)
January 2026 Microsoft Patch Tuesday Summary, (Tue, Jan 13th)
YARA-X 1.11.0 Release: Hash Function Warnings, (Sun, Jan 11th)
YARA-X's 1.11.0 release brings a new feature: hash function warnings.
When you write a YARA rule to match a cryptographic hash (either the full file content or a part of it), what's actually going on are string comparisons:
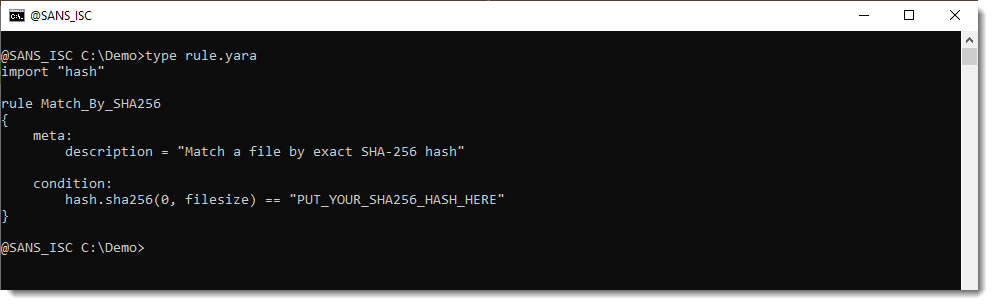
Function hash.sha256 returns a string (the hexadecimal SHA256 hash it calculated) and that is compared to a literal string that is the hash you want to find.
If you make a mistake in your literal string hash (for example: unintentionally add an extra space), then the match will fail.
But YARA-X will now show a warning like this:
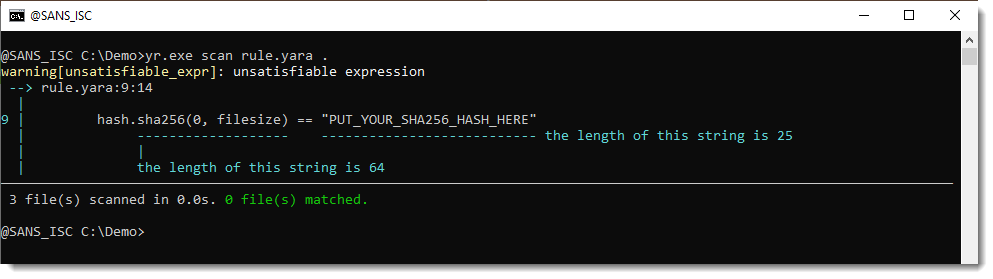
Another example is where you mixup hashes: you provide a SHA1 literal string hash, and it should be a SHA256.
Didier Stevens
Senior handler
blog.DidierStevens.com
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
Malicious Process Environment Block Manipulation, (Fri, Jan 9th)
Reverse engineers must have a good understanding of the environment where malware are executed (read: the operating system). In a previous diary, I talked about malicious code that could be executed when loading a DLL[1]. Today, I’ll show you how a malware can hide suspicious information related to created processes.
Analysis using Gephi with DShield Sensor Data, (Wed, Jan 7th)
I'm always looking for new ways of manipulating the data captured by my DShield sensor [1]. This time I used Gephi [2] and Graphiz [3] a popular and powerful tool for visualizing and exploring relationships between nodes, to examine the relationship between the source IP, filename and which sensor got a copy of the file. I queried the past 30 days of data stored in my ELK [4] database in Kibana using ES|QL [5][6] to query and export the data and import the result into Gephi.

![Battling Cryptojacking, Botnets, and IABs [Guest Diary], (Thu, Jan 15th)](https://www.ironcastle.net/wp-content/uploads/2026/01/status-7.gif)